7 of the best programming languages for cybersecurity (offensive & defensive)
An overview of the best programming languages to learn depending on the cybersecurity role you’re looking for.
Table of Contents
You may have heard how learning a programming language can increase your productivity, grow your skills, and boost your cyber career to the next level. But what languages should you take the time to actually learn?
This article will provide an overview of what programming languages you should focus on depending on the cybersecurity role you want to get into.
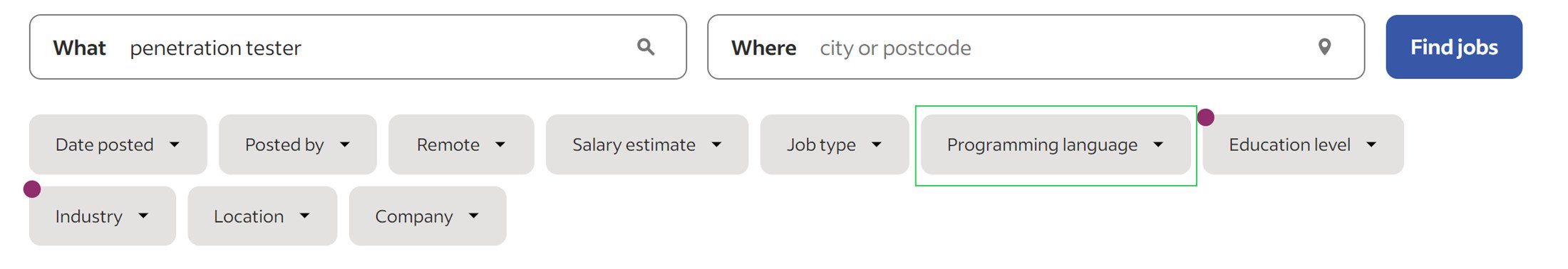
Almost every job posting for a cybersecurity position will list one or more programming languages as desired skills. Indeed has a nifty feature that lets you filter jobs by "Developer skill" (on select jobs).
Once you click this drop-down section in the "Find jobs" area of Indeed, you can see the most in-demand programming languages based on your search.
This gives you immediate feedback on what programming languages employers care about for the given position you are interested in, whether it's a penetration tester, cybersecurity analyst, cybersecurity engineer, incident responder, etc.
Using this filter on Indeed, the top five in-demand programming languages (at the time of writing) for cybersecurity analysts are:
1. Python.
2. PowerShell.
3. SQL.
4. Bash.
5. Perl.
And for penetration testers:
1. Python.
2. PowerShell.
3. Bash.
4. Java.
5. Ruby.
Recommended read: Secure coding practices for busy devs.
1. Python
Python is easily the most used programming language in cybersecurity. Every role benefits from knowing this prevalent and powerful programming language.
Cybersecurity blue teams widely utilize Python to automate security operations, analyze large datasets to detect threats, and create network monitoring and incident response tools.
The simplicity of Python, coupled with its extensive libraries, makes it an excellent language for tasks like log analysis and establishing security dashboards.
Moreover, blue team professionals can further use Python’s integration with popular security frameworks such as Scapy and PyCrypto to enhance their effectiveness.
On the other hand, red teams harness the power of Python to develop customized exploits, devise intricate attack scripts, and carry out penetration testing with Python's comprehensive network and security libraries like Scapy and Metasploit at their disposal.
Python's flexibility and user-friendliness make it an indispensable tool for red team professionals aiming to uncover weaknesses within an organization's security defenses while examining their resilience.
Real-world example: A Python script I wrote to take Nmap scan results and write all the open ports onto a single line separated by commas. This allows me to easily copy all open ports from the previous scan and paste them into the next command for more detailed Nmap scans using the -p option.
2. PowerShell
PowerShell plays a crucial role in Windows environments for both defensive and offensive security operations. It is a powerful automation tool for blue teams, allowing security analysts to automate tasks, verify system configurations, and conduct security assessments.
With its extensive command set, PowerShell aids in gathering system information, analyzing logs, detecting and investigating security incidents, and responding to threats.
It also provides access to Windows Management Instrumentation (WMI) for comprehensive system monitoring and management and Active Directory integration for effective user and access management.
On the offensive side, PowerShell's scripting capabilities make it a preferred choice for red teams and ethical hackers for Active Directory enumeration & attacks.
Its deep integration with Windows and access to system application programming interfaces (APIs) offer attackers avenues for privilege escalation and manipulation.
PowerShell is a formidable tool that empowers defensive and offensive security operations with efficient management, incident response, and simulated cyberattacks.
Real-world example: PowerShell commands I use during penetration tests and hacking labs:
powershell -c "Get-Service"
This command list all services running on the Windows target. Knowing the services running on the target allows you to determine potential attack vectors. As a defender, using this command reveals your attack surface, and can reveal potentially malicious services running on your end-point.
Get-ChildItem -Path C:\ -Include *[FILENAME]* -File -Recurse -ErrorAction SilentlyContinue
This command helps you find the location of a particular file on the target. This is especially useful in capture the flag (CTF) events when you generally know the name of the flag, but you may not know where it is stored.
Get-LocalUser
This command allows you to see all the users on the system.
Related read: Learn cybersecurity for free with HTB Academy.
3. Bash
Bash scripting is vital in cybersecurity, benefiting blue and red team operations. Bash is a versatile language with a comprehensive command set that enhances the capabilities of blue teams in areas such as:
-
Monitoring.
-
Anomaly detection.
-
Incident response.
-
Data parsing.
Blue teams utilize Bash's command-line interface and powerful tools like grep and awk to effectively manipulate and process large datasets. These capabilities enable them to create custom tools for log analysis, data extraction, and parsing, allowing for deeper insights into potential threats.
In red team operations, Bash proves its worth as a potent scripting language for offensive attacks.
It provides red teams the means to conduct reconnaissance, privilege escalation, lateral movement, and more. By leveraging Bash's command-line interface and abilities, red teams can exploit vulnerabilities, manipulate network traffic, and simulate real-world attack scenarios.
The versatility of Bash, combined with its widespread adoption, makes it an essential tool for cybersecurity professionals in any role. It empowers them to carry out tasks effectively and efficiently while upholding high standards of respect toward others in the field.
Real-world example: A Bash script I wrote that scans for open ports using the popular Socat tool. This Bash script is useful if you need to perform a portscan on a machine that has socat, but not Netcat, nc, or Nmap. This situation is very specific but I have seen it happen, which is why I made it.
4. Structured Query Language (SQL)
💡Note: SQL is not exactly a “programming” language, but rather a declarative language used to interact with specific relational databases. Still, learning SQL has a lot of similarities to learning programming languages.
SQL, a language used to query SQL or “relational” databases, is an indispensable tool for blue and red cybersecurity teams.
Defensive teams rely on SQL to effectively manage and analyze vast amounts of data, detect anomalies, and respond to security incidents.
By utilizing SQL's database interaction and data manipulation capabilities, they can correlate information across various sources and conduct thorough forensic investigations.
Red teams, on the other hand, use SQL to exploit database vulnerabilities, gain unauthorized access, manipulate data, and escalate privileges through SQL injection attacks.
Proficiency in SQL is crucial for success in both blue and red team scenarios as it allows professionals to navigate and manipulate databases to achieve their objectives.
Various flavors of SQL, such as MySQL, MSSQL, and PostgreSQL, support critical aspects of cybersecurity practices. It significantly strengthens database security measures, performs data analysis tasks, facilitates incident response activities, and identifies vulnerabilities.
With its versatility and widespread usage across the industry, SQL is fundamental in enhancing information security measures and overall cybersecurity practices.
Real-world example: A massive list of common SQL injection payloads that I frequently use in penetration tests and hacking labs. Simple queries such as these can often bypass login screens to applications that don’t properly sanitize user input:
' OR '1
' OR 1 -- -
" OR "" = "
" OR 1 = 1 -- -
' OR '' = '
'='
'LIKE'
'=0--+
OR 1=1
5. Java
Java is a general-purpose programming language that’s commonly used for developing software, applications, and even server-side technologies across most platforms and industries.
Defensive security professionals harness the object-oriented characteristics of Java, as well as its extensive libraries, to craft robust security tools, perform meticulous log analyses, and exercise diligence in monitoring network traffic.
This empowers them to design and implement secure applications that function across diverse operating systems—a crucial advantage that supports incident response activities such as malware analysis or forensic investigations.
Conversely, red team practitioners skillfully exploit the cross-platform compatibility of Java to their advantage by designing and deploying malicious software and exploiting code. This means they can target various systems while evading established security measures.
Supported by the rich ecosystem of Java, red teams have access to many different tools specifically designed for network scanning purposes or for executing post-exploitation tasks.
Real-world example: An open-source automated Java SQL injection tool that can automate the entries of common SQL injection payloads written in Java. This tool can vastly improve the speed of any security assessment looking for SQL injection vulnerabilities.
6. Perl
Perl initially focused on text processing but has transformed into a versatile programming language suitable for multiple applications.
Its notable attributes include strong text processing abilities, extensive support for system administration tasks, and the capability to handle diverse programming requirements such as web and application development, networking operations, and data manipulation.
With its robust text processing capabilities, blue teams rely on Perl for various security tasks, such as log analysis, network scanning, and system monitoring.
Perl is ideal for parsing and extracting valuable information from large data sets. Blue teams also use Perl to automate repetitive tasks, develop security tools, and conduct vulnerability assessments.
For red teams, Perl can be a powerful scripting language that facilitates offensive security operations. Its flexibility and extensive libraries enable red teams to create sophisticated attack scripts and exploit vulnerabilities effectively.
By leveraging Perl's regular expression support and powerful string manipulation features, red teams can craft and execute attacks, including code injection and reconnaissance. Moreover, Perl's ability to interact with databases allows red teams to manipulate and extract sensitive information during operations.
Real-world example: The LFI to RCE Exploit with Perl Script is a public exploit that targets a vulnerability known as Local File Inclusion (LFI) to achieve Remote Command Execution (RCE) on a specific system.
It involves injecting malicious code into a website, enabling attackers to manipulate the application and include files from the local file system. As a result, arbitrary commands may be executed, granting unauthorized access, data manipulation, and privilege escalation on the target system.
7. Ruby
Ruby is highly regarded as a flexible programming language, often praised for its simplicity and readability. Particularly in web development, it shines with frameworks like Ruby on Rails.
Additionally, it is an exceptional tool for scripting, prototyping, data analysis, and system administration. The critical factor behind Ruby's popularity lies in its emphasis on ensuring developer satisfaction and its elegant syntax, making it an attractive choice for numerous applications.
The straightforward structure of Ruby allows for efficient log analysis, reliable network scanning, and system activity monitoring. Blue teams also find value in using libraries and frameworks to optimize productivity by automating tasks and customizing security solutions for incidents.
On the other hand, red teams take advantage of Ruby's unique features and libraries within the widely-used penetration testing framework, Metasploit. By merging Ruby with Metasploit, red teams gain access to powerful tools to exploit vulnerabilities and infiltrate systems.
The concise language structure of Ruby, alongside its metaprogramming capabilities and seamless database integration, enables red teams to quickly create versatile attack tools that manipulate critical information during penetration tests.
Real-world example: Ruby code that is the foundation of Metasploit's capabilities. This code enables security professionals and ethical hackers to delve into and investigate the inner workings of the framework.
By doing so, they can gain valuable knowledge on advanced exploitation techniques and make meaningful contributions to cybersecurity's continuous growth and innovation.
Honorable mentions
Other prevalent programming languages include JavaScript, C, C++, C#, PHP, Assembly, and VBA.
Learning your first programming language for cybersecurity
I would recommend starting with Python as a first language as it is simple to learn and popular.
From there, you don't necessarily need to dedicate much time to the other programming languages to be effective with them.
For example, I dedicated 100 days to learning Python. However, I still learned how to use Bash, PowerShell, SQL, JavaScript, PHP, C#, VBA, Ruby, and Perl effectively through certification exams and pwning various Hack The Box Machines.
Besides Bash and Python, I've never created a program in these languages from scratch. However, as a penetration tester and CTF player, I have successfully exploited in-scope targets with all of these languages.
So don't get caught up and overwhelmed with mastering every programming language on this list. Get very familiar with one or two, and you can find success with the rest.
|
Author bio: Kyser Clark (KyserClark), Cyber Defense Operations (1D771), United States Air Force (Active duty) Kyser is a Cyber Defense Operations leader with over 5+ years of active duty U.S. Air Force experience specializing in offensive security, ethical hacking, penetration testing, and red teaming. His credentials include a Bachelor of Science (BS) in Cybersecurity Management & Policy from the University of Maryland Global Campus (UMGC), and 11 industry certifications: OffSec Certified Professional (OSCP), (ISC)² Certified Information Systems Security Professional (CISSP), eLearnSecurity Junior Penetration Tester (eJPT), EC-Council Certified Ethical Hacker (CEH), Cisco Certified Network Associate (CCNA), CompTIA PenTest+, Cybersecurity Analyst (CySA+), Cloud+, Linux+, Security+, and Network+. Kyser encourages you to connect with him in these places in cyberspace: |