How cyber workforce assessments boost business-critical operations
Learn how to capitalize on the outcomes of your CTF events and build a comprehensive, long-term workforce development plan.
Table of Contents
Back in 2021, the team at Toyota Motors North America reached out to us with a challenge.
We discovered after a couple of calls and consultations that it was way more than just a challenge: Gabe Lawrence, the VP of Information Security Cyber Protection at Toyota, was looking for hands-on and dynamic training for this team.
No sweat, we thought. Upskilling cyber teams is our bread and butter at Hack The Box (HTB); we’ve provided one of the best threat-connected security solutions in the industry since 2017.
However, it turned out that the Toyota team was looking for way more than help with upskilling its team. They were looking to achieve critical business goals by benchmarking, assessing, and developing the skills of each team member.
Gabe identified the following as fundamental objectives for his security department:
-
Bridge the knowledge gap between security and cloud teams.
-
Foster team collaboration and support.
-
Stay updated with the latest vectors and techniques.
-
Specialize blue teamers and SOC analysts.
-
Align hiring strategies to skill gaps.
But more importantly, he addressed the need of having a clear, transparent analysis of the current skills of his team—with a defined roadmap on how to fill potential gaps and reach the desired state.
Gabe’s challenge of quantifying skills gaps to develop Toyota’s cyber team is common amongst security leaders. We’ve noticed that the solution usually boils down to a smooth system for assessing skills and identifying the next steps based on industry requirements.
In this post, we’ll share practical tips inspired by Gabe’s story and other successful security teams. You’ll learn how they use assessments to benchmark skills and strategically develop cyber workforce capabilities.
Why it’s not always easy to know your team
The practices of benchmarking team capabilities and gap analysis are vital to enable technical leaders to design a workforce development plan.
Benchmarking mostly involves assessing the performance, skills, and effectiveness of a cybersecurity team against industry standards or best practices. This helps organizations understand how well their team aligns with the current requirements of the threat landscape.
Gap analysis is more focused on identifying the lack between the current state of a cybersecurity team's capabilities and the desired or required state. It involves evaluating existing skills, processes, and technologies against predefined company goals to identify areas for improvement.
Seems pretty straightforward, right? “Know your team,” they say.
Like many things in cyber, it’s easier said than done. Organizations are struggling to implement a data-driven approach to these practices or connect the results with concrete next steps. This evolving nature of cybersecurity carries some blame, but it’s not the only factor making skills assessment and workforce planning tougher.
Diversity of cybersecurity roles
Cybersecurity teams consist of professionals with diverse roles, responsibilities, and skills. Designing a standardized skills assessment process that caters to the unique requirements of each role is challenging, not always effective, and time-consuming.
Managers must possess the ability to easily customize and tailor their workforce development plans based on constantly changing goals, objectives, and team needs.
Lack of standardized metrics
When it comes to skills and capabilities, organizations find it challenging to compare their teams with industry benchmarks and foster collaboration due to variations in measurement criteria.
On the other hand, security leaders are tasked to report relevant security metrics with a clear view on how these impact business metrics.
Employee skill development
Teams may face difficulty in addressing skill gaps identified through benchmarking due to limited resources for training and development or low engagement. Security leaders are the ones driving the change to a shared upskilling culture by adopting the right processes, training materials, and assessments.
Limited visibility into threats
Organizations may lack visibility into current and emerging threats, while cybercriminals train on production systems. This makes it crucial to provide cyber defenders with a threat-connected upskilling solution: without a comprehensive understanding of threat vectors, assessment and benchmarking efforts may be misguided, leading to inaccurate gap analysis.
The importance of regular assessments
With more visibility into the business needs and the related challenges, it’s clear that regular assessments are fundamental in a business aiming to build a resilient cybersecurity workforce.
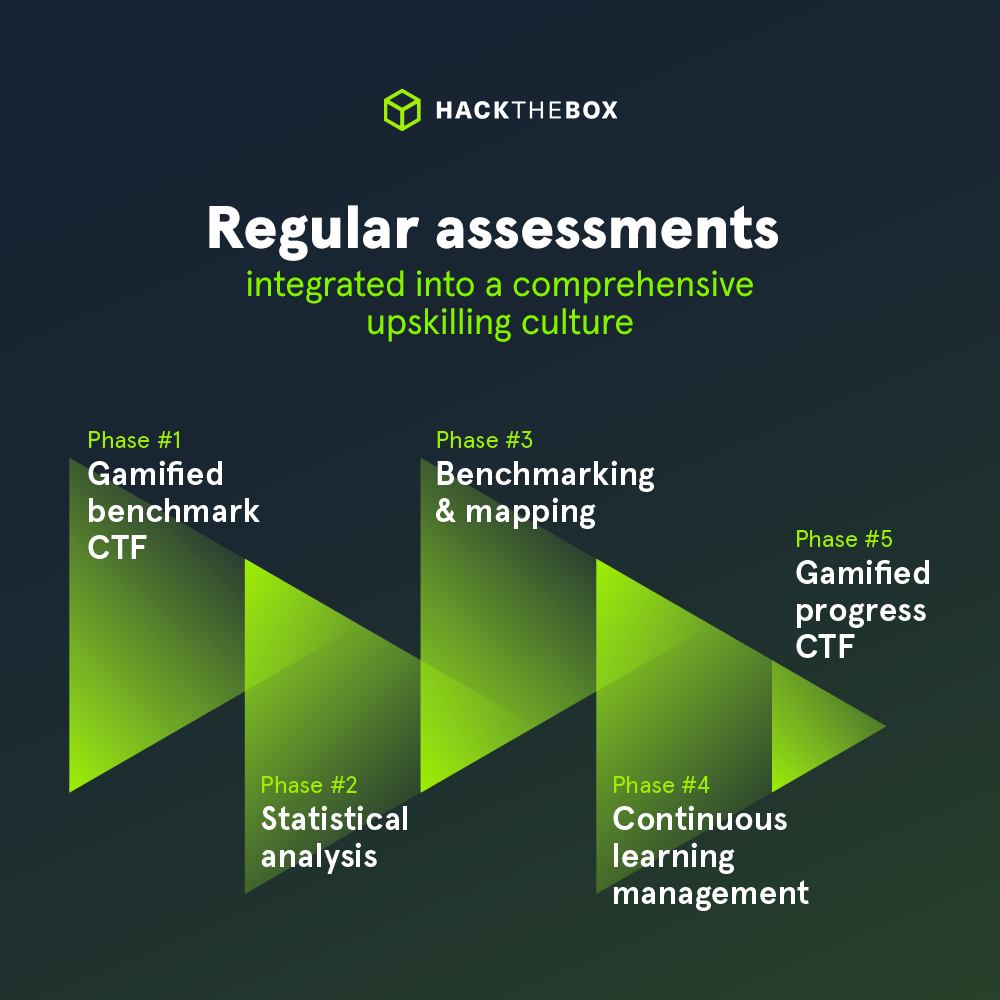
By using the training materials and features available on Hack The Box, we have crafted a unique 5-step methodology to help our customers optimize resource allocation, enhance incident response operations, foster a collaborative culture, and improve critical business functions.
Step #1: Gamified benchmark CTF
Capture The Flag events are the perfect way to evaluate the current performance while ensuring engagement and collaboration. Using our CTF Marketplace, teams have great flexibility in selecting between a wide range of hands-on scenarios (offensive, defensive, cloud, and more) directly from our library, or utilizing pre-packaged packs aligned to security roles or knowledge domains.
💡 Not only content selection: our CTF platform provides seamless event coordination features to enable the maximum level of customization and gamification.
Step #2: Data-driven analysis
After the CTF is completed, managers can access a detailed statistical report about the team’s performance and outcomes. The report can be visualized on a member, team, or organizational level with specific insights on content completion, techniques implemented, and difficulty level.
As an example, while analyzing performance, managers may notice that over 80% of team members completed Challenges in Forensics, Blockchain, or Web categories. However, if a much smaller percentage of the team completed Challenges in Reversing category, this provides you an opportunity to assign relevant content in that skill area using Academy.
Step #3: Benchmarking & mapping
We now have a clear view of the team’s capabilities and its gaps. In other words, we have clearly identified where our team stands.
These results can now be mapped against the most relevant security frameworks, such as MITRE ATT&CK or NIST/NICE, to discover where to focus the upskilling efforts and connect them with relevant company goals.
Step #4: Continuous learning management
How do we move from the current state to the desired state?
The focus should now shift to creating a curated learning path based on the gaps identified. Leveraging the detailed content categorization available on HTB Enterprise Platform, managers can create a comprehensive workforce development plan by selecting between 1,000+ courses and labs directly covering the needs discovered.
In addition to an expanded content library, managers can efficiently use exclusive features and dashboards unlocking reporting capabilities, completion insights, skill progression, activity over time, and lab management.
Step #5: Gamified progress CTF
The gamified progress CTF allows individuals and teams alike to showcase the new skills they have acquired against real-life scenarios. A post-CTF analysis can be compiled to demonstrate to the board the investments in skills compared to incident risk reduction, or contribute to other business operations such as hiring priorities or security champion programs.
Benchmark to avoid burnout
What if regular skill assessments could also be the not-so-secret solution to better retain cybersecurity employees?
Based on our annual benchmarking report of 803 security professionals, more than 70% of managers view team events like CTFs as a viable way to raise employee engagement, while 72% agree that CTF events can help measure and upskill employees.
Hack The Box enables security leaders to sharpen skills and build specialized teams with a suite of cyber workforce upskilling solutions.
Given current economic uncertainty, dwindling security budgets, and rampant burnout, team events can maximize ROI on limited training budgets and boost motivation to perform.
Choose HTB to boost your cyber performance
Today’s cyber threats present a new challenge to organizations, and unskilled teams pose a real risk to the security of your business. This is why cybersecurity performance programs and continuous improvement are no longer a nice-to-have, but a necessity.
Where is your team standing? It might be the perfect time to find out. Like Toyota, any organization can achieve crucial security goals by implementing accurate (and effective) benchmarking or assessment practices.
-
Risk mitigation: Timely content offers training on the latest CVEs in real-world environments, reducing risk and exposure to these vulnerabilities.
-
Employee retention: Cybersecurity teams that are offered upskilling opportunities are far more engaged and less likely to burn out.
-
Performance benchmarking: Conduct CTFs and gap analysis to identify weaknesses in your security posture.
-
Tailored training to industry standards: HTB content is mapped to MITRE ATT&CK and NIST NICE frameworks so you can assess your cyber preparedness in different areas.
-
Boost organizational awareness: HTB can assess cyber readiness and performance company-wide with effective practices like tabletop exercises (TTXs) or nearly practical assessments designed for security staff and non-technical teams.