Quantify and manage your cyber risk exposure
Think like attackers—simulate threats, track progress and prove readiness with courses, ranges, or team exercises.

%20(1).png)
%201%20(1).png)
Trusted by 1,000+ cybersecurity teams
-1.png)
Why offensive skills matter now
14%
Of companies have in-house exploit expertise to meet today’s threat landscape.
3x
Skill gaps triple mean time to respond, extending breach impact windows and costs.
35%
Decrease in risk and security incidents with threat-led pentesting programs in place.
Hands-on-first learning methodology
Our platform focuses on practical skills development in real-world environments, not theoretical knowledge that doesn't transfer to actual red team engagements.
3x
Faster ramping time for new hires
90%
MITRE and NIST coverage in 6 months
50%
Decrease in time patching CVEs

Full-scope adversary
Replicate full kill chains, from open-source recon to final data exfiltration, to understand how early actions cascade into business critical impact.

Continuous skill measurement
Use advanced reporting and analytics to have accurate, real-time visibility into teams’ skill proficiency at any time. Identify critical gaps and build future plans.

Framework alignment
All our content library maps to NIST and MITRE frameworks, ensuring your team builds skills keeping up with the threat landscape and regulatory requirements.
How red teamers use Hack The Box
Penetration Testers
Training Plans

Combine job role paths with more than 1,200 labs simulating the latest security vulnerabilities and vectors, with new scenarios added every week.
Ranges

Team Assessments

Training Plans
Ranges
Team Assessments
Combine job role paths with more than 1,200 labs simulating the latest security vulnerabilities and vectors, with new scenarios added every week.
Red Team Operators
Training Plans

Use 1,000+ courses and labs to progress from fundamentals to advanced adversary emulation while learning how to adopt new technologies in your engagement - including AI.
Ranges

Team Assessments

Training Plans
Ranges
Team Assessments
Use 1,000+ courses and labs to progress from fundamentals to advanced adversary emulation while learning how to adopt new technologies in your engagement - including AI.
Malware & Exploit Developers
Training Plans

Combine threat-informed courses with CVE scenarios and learn how to conduct penetration tests against modern and highly secure applications.
Ranges

Team Assessments

Training Plans
Ranges
Team Assessments
Combine threat-informed courses with CVE scenarios and learn how to conduct penetration tests against modern and highly secure applications.
AI & ML
Introduction to Red Teaming with AI
Overview the common security vulnerabilities in systems deploying AI and the types of attacks that can be launched against their components.
key skills
- Generative AI
- ML Systems
- LLM OWASP
INTERMEDIATE
Offshore
Real-world enterprise attack simulation that features a wide range of modern Active Directory misconfigurations and adversarial techniques.
key skills
- Web Applications
- Enumeration
- Active Directory
MEDIUM
Penetration Testing – Essentials
10 scenarios for a 2-day team assessment to understand how attackers breach enterprise networks and how to defend against them.
key skills
- CVEs
- Privilege Escalation
- LLM OWASP
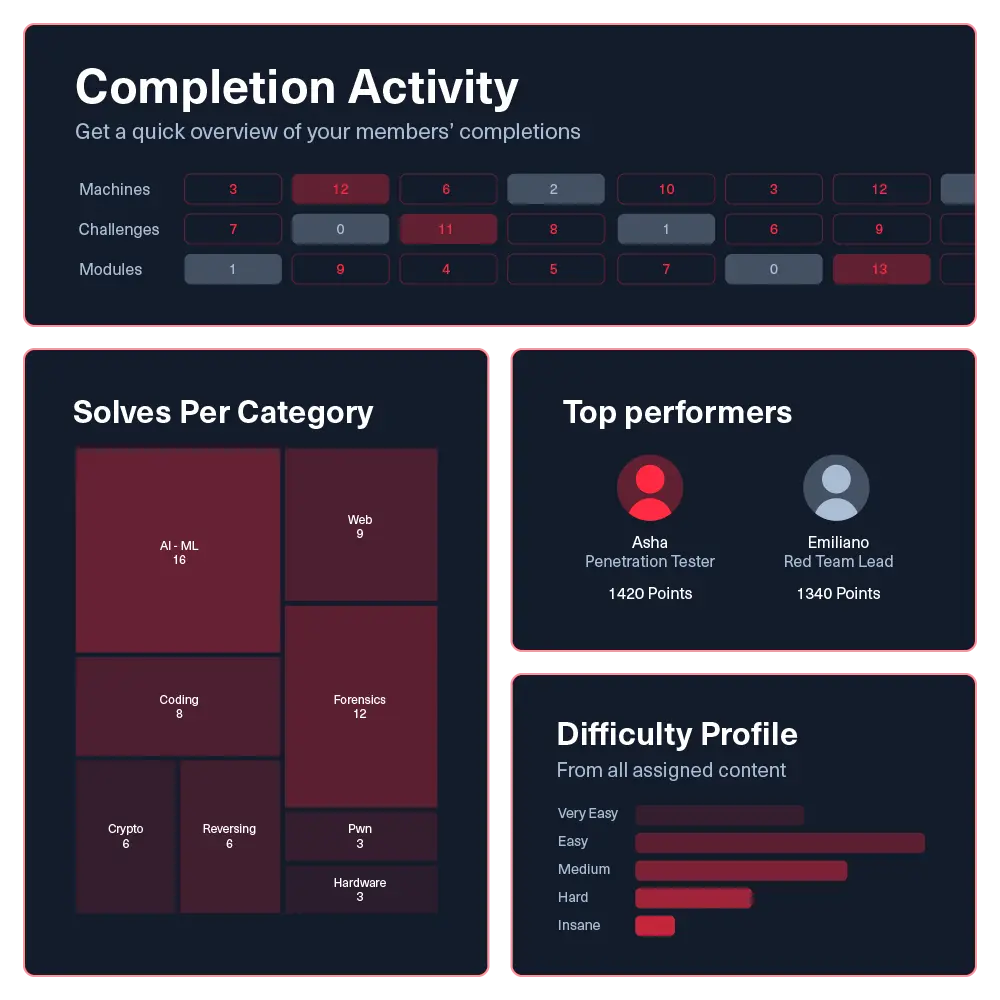
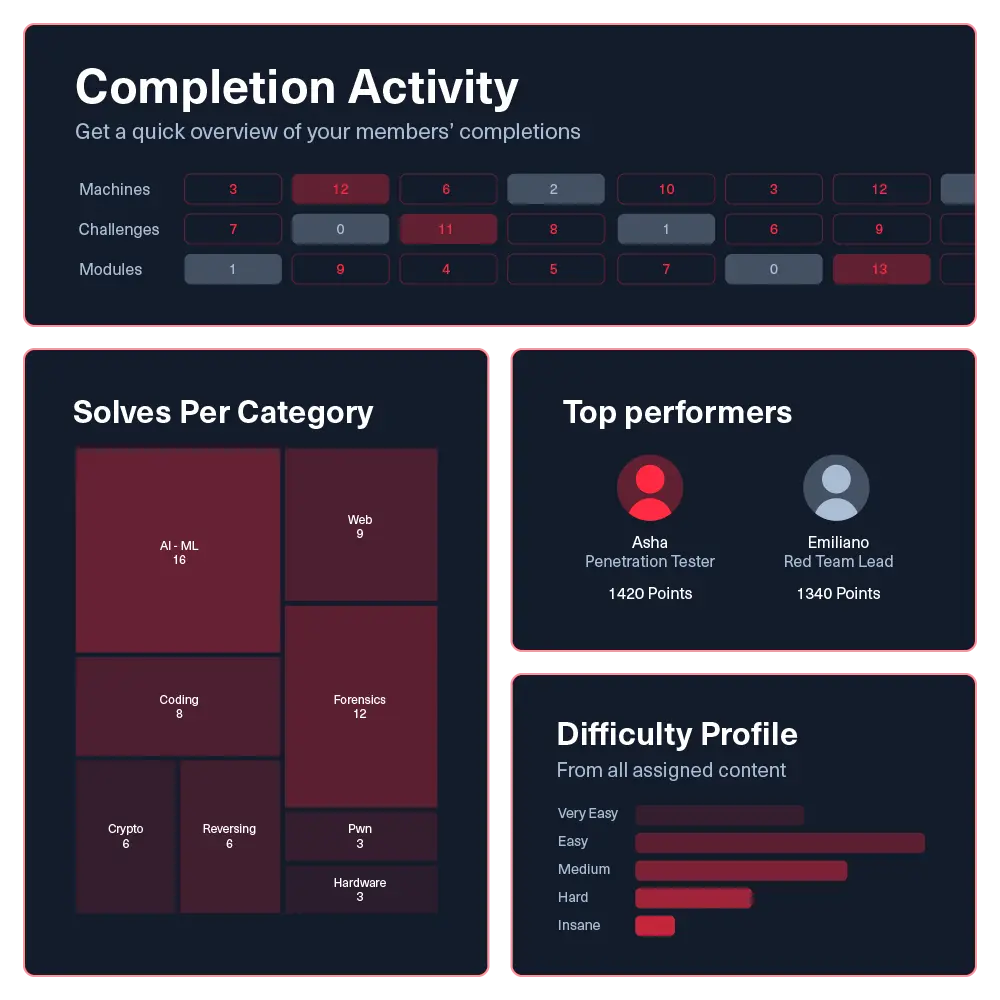
Data-driven cyber resilience
Measure security team performance with reporting features that demonstrate skill growth and operational readiness.
Individual & team analytics

Track key metrics like MTTD, alert precision, and investigation quality at both the individual and team level.
Skill coverage heatmaps

Customization and integration

Individual & team analytics
Skill coverage heatmaps
Customization and integration
Track key metrics like MTTD, alert precision, and investigation quality at both the individual and team level.
How major global organizations stay ahead of threats
For cybersecurity enthusiasts
HTB gamified labs walk newcomers through the entire kill-chain (from recon to privilege escalation) so they internalize real adversarial techniques and gain a threat-ready mindset.
For cybersecurity professionals
Seasoned red teamers can replay APT playbooks, develop custom C2 profiles, and measure skill progression, sharpening threat readiness while expanding their arsenal of tactics, techniques, and procedures.
For managers & technical leaders
Role-based analytics, ATT&CK heat-maps, and skill gap reports give leaders clear proof of red team maturity, enabling targeted programs that validates adversary coverage and reduces organizational risk exposure.

HTB has given us the ability to rapidly respond to changes in our required skillset. If leadership shifts priorities, for example if they say we need to focus on API security, we can immediately direct the team to relevant modules and upskill in a timely manner. It saves us the time of sourcing and negotiating, making us more agile and effective.
%20(1).png)
Get a full demo with our team
Fill the form to schedule a live product demo and Q&A about our cyber readiness solutions.
The #1 platform to build attack-ready teams and organizations
Maximum curriculum management flexibility, enhanced skills reporting, and engaging gamification features. Book a demo to get the business results.
Your plan includes:
- ✓ Unmatched content library
- ✓ Workforce development plans
- ✓ Centralized user management
- ✓ Advanced analytics & reporting
- ✓ Source, hire, and retain talent



