Offensive exercises to enable predictive defensive operations
Break the silos between red & blue teams to ensure enhanced detection, risk mitigation, and threat-ready incident response plans.

%20(1).png)
%201%20(1).png)
Trusted by 1,000+ cybersecurity teams
Turn threat intelligence into actions
60%
Of ATT&CK and adversary techniques left unmonitored with siloed security teams.
10+
The estimated dwell time (in days) forattacks without proactive detection.
$10m
The possible regulatory fines for missing mandatory threat-led penetration testing.
Threat-informed learning model
Our platform focuses on practical skills development in real-world environments, not theoretical knowledge that doesn't transfer to actual cyber operations.
3x
Faster ramping time for new hires
90%
MITRE and NIST coverage in 6 months
50%
Decrease in time patching CVEs
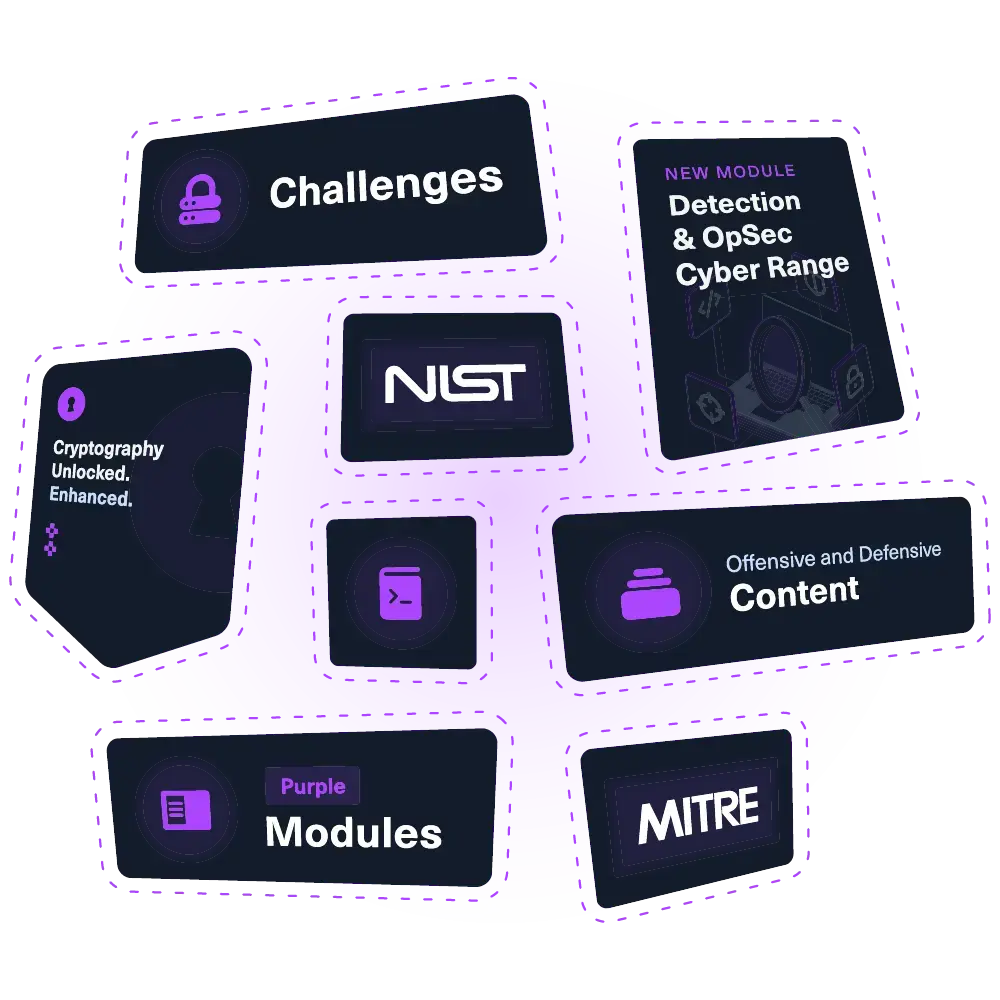
Threat emulation
Build intelligence-driven exercises and emulate TTPs executed by real adversaries: Scattered Spider, Salt Typhoon, Mustang Panda, or any other APT group.
Continuous skill measurement
Build intelligence-driven exercises and emulate TTPs executed by real adversaries: Scattered Spider, Salt Typhoon, Mustang Panda, or any other APT group.
Team collaboration
Red and blue teams can collaborate in real-time using gamified, live-fire labs, ranges or simulations. Execute, respond, and keep track with real-time telemetry.
How purple teams use Hack The Box
Purple Team Operators
Training Plans

Chain red team TTP courses with detection engineering labs, guiding analysts from threat intel mapping to automated rule testing while the platform tracks progress real-time.
Ranges

Team Assessments

Training Plans
Ranges
Team Assessments
Chain red team TTP courses with detection engineering labs, guiding analysts from threat intel mapping to automated rule testing while the platform tracks progress real-time.
Adversary Emulation Engineers
Training Plans

Combine advanced OpSec, custom C2 development and threat intel labs, so practitioners learn to emulate realistic APT campaigns in a safe environment and ensure readiness.
Ranges

Team Assessments

Training Plans
Ranges
Team Assessments
Combine advanced OpSec, custom C2 development and threat intel labs, so practitioners learn to emulate realistic APT campaigns in a safe environment and ensure readiness.
Detection Engineers
Training Plans

The detection engineering job role path guides analysts through advanced detection workflows and ATT&CK coverage, combined with more than 1,000+ hands-on labs.
Ranges

Team Assessments

Training Plans
Ranges
Team Assessments
The detection engineering job role path guides analysts through advanced detection workflows and ATT&CK coverage, combined with more than 1,000+ hands-on labs.
RANGE
Windows Attack & Defense
Cover the commonly performed attacks by threat actors. Learn prevention and detection methods against Active Directory environments.
key skills
- Kerberoasting
- Active Directory
- Event Logs
APT
HorsePanda & HorsePanda-D
Test or defend systems against Mustang Panda's techniques combing offensive and defensive scenarios based on their attack campaigns
key skills
- Malware Analysis
- Nation State
- Phishing
BEGINNER
Malware Reversing - Essentials
A 2-day team assessment to cover adversary-level insights, improving defensive strategies, amlware triage, and forensic investigations.
key skills
- Threat Hunting
- Incident Response
- Detection
Data-driven cyber resilience
Measure security team performance with reporting features that demonstrate skill growth and operational readiness.
Individual & team analytics

Track key metrics like MTTD, alert precision, and investigation quality at both the individual and team level.
.webp)
Skill coverage heatmaps

Customization and integration

Individual & team analytics
Skill coverage heatmaps
Customization and integration
Track key metrics like MTTD, alert precision, and investigation quality at both the individual and team level.
.webp)
How major global organizations stay ahead of threats
For cybersecurity enthusiasts
Hands-on purple team labs let newcomers play both attacker and defender in the same scenario, revealing how real-time collaboration slashes blind spots and turns theory into tangible risk reduction.
For cybersecurity professionals
Enterprise-scale ranges stream live adversary actions into SIEM/EDR dashboards while analysts tune detection rules, creating predictive actions that shrink MTTD and prove collaboration that drives down breach risk.
For managers & technical leaders
New regulatory frameworks now require organizations to demonstrate enhanced detection capabilities. Without modern solutions, teams face increasing pressure and diminishing effectiveness. Fully control your team's cyber readiness.
The best defense is a good offensive mindset. Hack The box has enabled our security engineers a deeper understanding on how adversaries work in a real world environment. With HTB, we can learn at your own pace and track progress towards readiness. I've seen the knowledge of exploitation, privilege escalation, and system enumeration grow exponentially.

Get a full demo with our team
Fill the form to schedule a live product demo and Q&A about our cyber readiness solutions.
The #1 platform to build attack-ready teams and organizations
Maximum curriculum management flexibility, enhanced skills reporting, and engaging gamification features. Book a demo to get the business results.
Your plan includes:
- ✓ Unmatched content library
- ✓ Workforce development plans
- ✓ Centralized user management
- ✓ Advanced analytics & reporting
- ✓ Source, hire, and retain talent



