Cybersecurity awareness: A (simple) cheat sheet for staying safe
Improve your cybersecurity awareness with this simple and effective cheat sheet for defending yourself against digital attacks.
Table of Contents
Identity theft. Financial fraud. Malicious malware. Ransomware.
Whether you're a seasoned cybersecurity professional, a cautious computer user, or even a digital daredevil, today’s cyber threats are undeniably scary, aren’t they?
Well, only if you’re unaware of how to detect and protect yourself from them!
In this post, we’re arming you with a simple (but powerful) cybersecurity cheat sheet to face cybercrime head-on and defend against dastardly digital attacks.
Cybersecurity awareness (train yourself to spot attacks)
Verizon’s 2022 Data Breaches Investigations Report revealed that 82% of data breaches involved a human element. This includes incidents in which employees expose information directly (e.g. misconfiguring databases) or fall prey to social engineering attacks and other mistakes that enable cybercriminals to infiltrate systems.
Cybersecurity can seem like a complex subject, but at its core, it’s all about people. That’s why staying safe online starts with raising your basic level of awareness and understanding of different cyber threats.
This is the main goal behind Cybersecurity Awareness Month, the annual initiative hosted every October by the US government and private industry to empower everyone to protect themselves and their data from digital crime.
So without further ado, let’s move on to the most important attacks to be aware of in 2022 (and how to defend yourself)!
Phishing scams
Phishing is a sneaky type of social engineering attack used to steal data such as cookies or personal information like login credentials and credit card numbers (socially engineered attacks rely heavily on human interaction and often involve manipulating people).
Acting as a trusted entity or person, an attacker will use realistic email, text, or social messages to lure victims into clicking on malicious links or accidentally handing over sensitive personal information.
How to spot a phishing attack
Phishing attacks are a special type of sinister due to their deceptiveness.
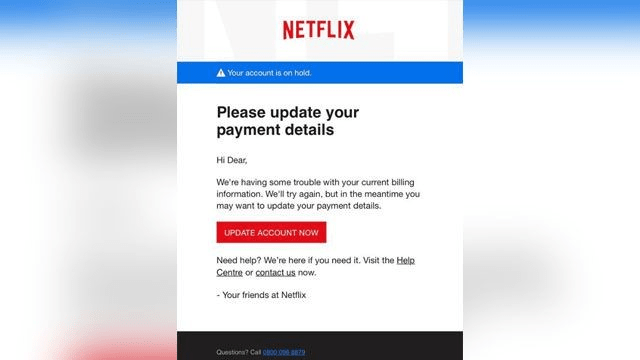
We’d all be weary of receiving an email from a random stranger who (for some strange reason) wants to store money in our bank account and requires our account details. Today’s phishing scams, however, are more cunning and appear to come from trusted and popular sources. Malicious hackers and scammers will mimic an official brand’s logos and email domains, and make urgent requests to dupe unaware victims into thinking the message is authentic.
The key to defending against them is to know the tell-tale signs and messages:
-
Request to log in or update payment information messages: Suggest that they’ve updated login credential policies or require up-to-date payment details. Targets are encouraged to update and submit details in order to avoid account deactivation or losing access to a product or service.
-
Fake invoices and delivery confirmation: Notify targets of pending payments for fake purchases or confirmation of phony goods. They rely on urgency and fear to get victims to click links or download documents.
-
Tax alerts: Prey on tax-related fears. These high-pressure scams coax users into submitting “overdue” payments and personal tax information. They’re especially prevalent around tax season.
-
Social media message: Share seemingly innocent invitations to watch videos or click links that install malware capable of corrupting devices and compromising personal data.
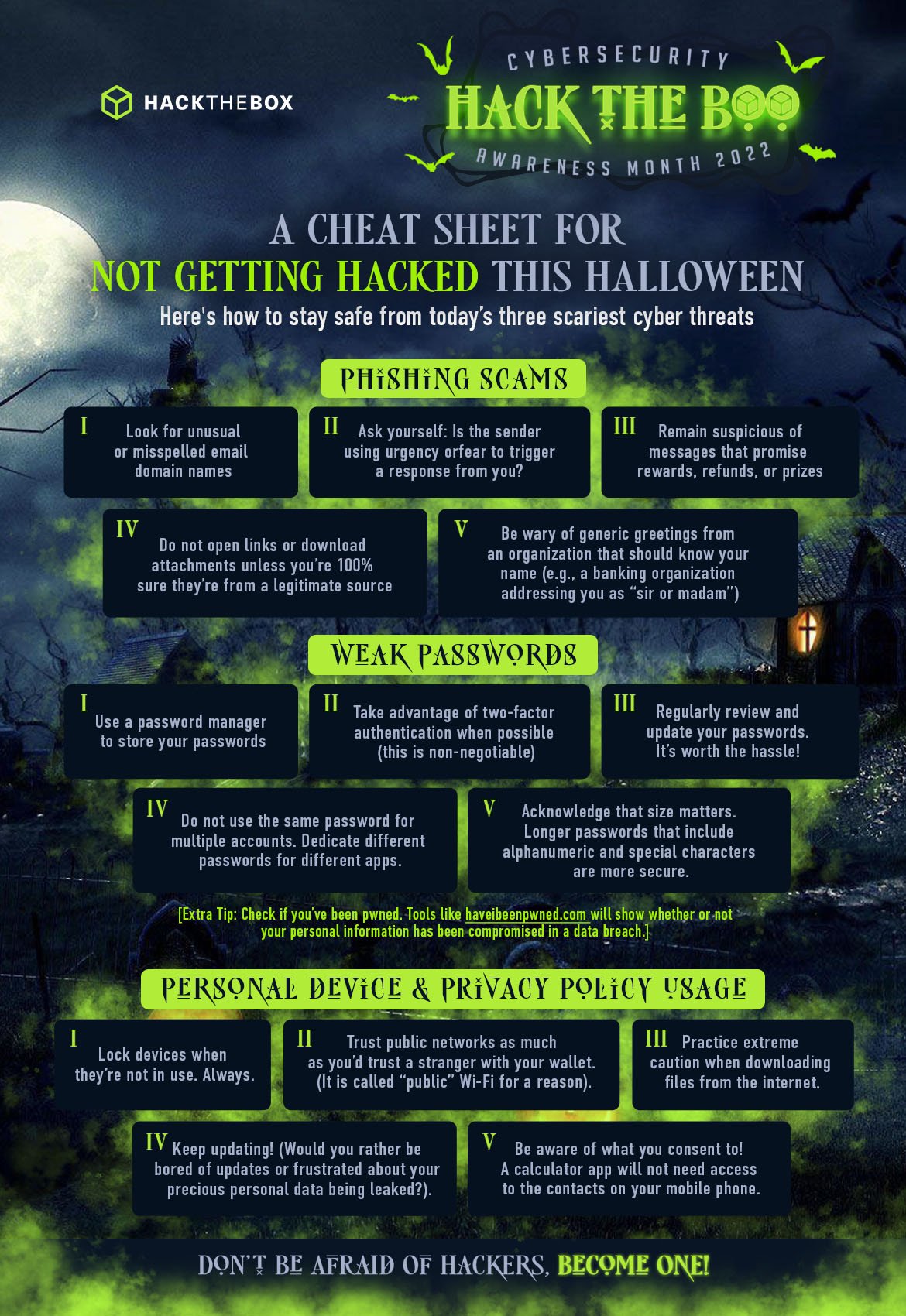
To protect yourself from phishing attacks:
-
Look for unusual or misspelled email domain names.
-
Do not open links or download attachments unless you’re 100% sure they’re from a legitimate source.
-
Ask yourself: Is the sender using urgency or fear to trigger a response from you?
-
Be wary of generic greetings from an organization that should know your name (e.g. a banking organization addressing you as “sir or madam”).
-
Remain suspicious of messages that promise rewards, refunds, or prizes.
Weak passwords
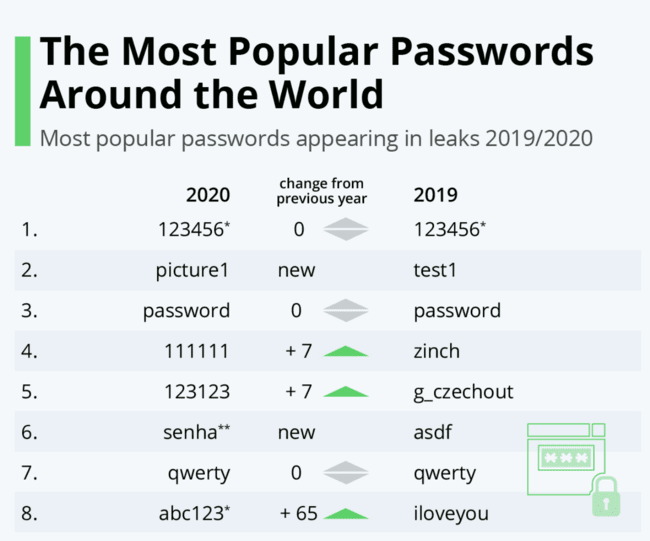
In 2020, hackers believed to be operating on behalf of the Russian government breached the IT software provider SolarWinds, deploying a destructive malware-laced update that infiltrated at least 18,000 US government and private networks.
While this is a shocking breach, what's even more surprising is that the breach may have been caused by an intern using "'solarwinds123" for an important password.
To protect yourself against breaches created by weak passwords:
-
Regularly review and update your passwords. It’s worth the hassle!
-
Take advantage of two-factor authentication when possible (this is non-negotiable).
-
Do not use the same password for multiple accounts. Dedicate different passwords for different apps.
-
Acknowledge that size matters. Longer passwords that include alphanumeric and special characters are more secure.
-
Use a password manager to store your passwords.
-
Check if you’ve been pwned. Tools like Have I Been Pwned will show whether or not your personal information has been compromised in a data breach.
Personal device and privacy policy usage
When a consumer research platform Which? set up an experimental smart home, its researchers were blown away by the barrage of cyberattacks against the home and the smart devices it housed: 14 attempts every single hour.
While incoming attacks targeting your home devices are a scary thought, they aren’t the only threats to be vigilant of. A lack of cybersecurity awareness when using personal devices in public can also drastically increase your vulnerability to an attack.
Walter Slootbon gained access to a selection of customer devices in a busy cafe with just a laptop and a hacking device that mimicked the cafe's Wi-Fi network, and then redirected all internet traffic through his device.
Eventually, his laptop displayed the activity of other devices people were using in the café. He was even able to intercept passwords with fake web pages (DNS Spoofing) and scan devices for names, passwords, and even sexual orientation.
Fortunately, Slotboon is a cybersecurity enthusiast hacker who didn’t leak or compromise user information. He conducted the experiment to highlight the dangers driven by a lack of cybersecurity awareness.
To keep your devices secure at home and in public:
-
Trust public networks as much as you’d trust a stranger with your wallet. (It is called “public” Wi-Fi for a reason).
-
Lock devices when they’re not in use. Always.
-
Keep updating! (Would you rather be bored of updates or frustrated about your precious personal data being leaked?).
-
Be aware of what you consent to! A calculator app, for example, will not need access to the contacts on your mobile phone.
-
Practice extreme caution when downloading files from the internet.
Don’t be afraid of hackers. Become one!
Practicing the steps above will raise your awareness of cyber threats and go a long way in protecting you from tenacious attackers. But why stop there?
Let us guide you on your journey to becoming a hacker (or at least understanding the basics!) in our beginner-friendly free Starting Point lab. If you like it, you can subscribe to our VIP+ package to access all Starting Point Machines and their Write-ups among other perks (like unlimited access to a browser-based virtual hacking distro pre-installed with all the tools you need to start hacking).
25% off the VIP+ subscription
Our motto this Cyber Awareness Month is “Don’t be afraid of hackers. Become one!” So we’re providing everyone with the perfect means to practice! Get 25% off on our annual VIP+ subscription (until October 31, 23:59 UTC) by using the code hacktheboo at checkout.
If you’re looking for a guided learning experience, we’ve also got you covered! The HTB Academy is a great place to start with free courses on how the internet works and more comprehensive beginner-advanced online courses about offensive, defensive, or general cybersecurity fundamentals.