7 powerful pentesting tools (& why you should stop pedestalizing them)
Practical resources for understanding the applications and techniques behind common pentesting tools.
Table of Contents
Reading this list of tools isn’t going to turn you into an Nmap master anytime soon. More importantly, becoming an Nmap, Burp Suite, Linux, or [insert pentesting tool] master alone won’t make you a better pentester.
This is because over-relying on tools may inhibit problem-solving skills that underpin the art of hacking: out-of-the-box thinking, creativity, and persistence.
For example, if you don’t understand how web requests and web applications work, but know that Burp Suite or Nikto both test for web app vulnerabilities, you’ll struggle in real-world assessments because you don’t understand the “backend.”
That’s why this list pairs common pentesting tools with practical resources for understanding the applications and techniques behind each tool.
💡Note: You can practice the fundamental techniques behind most of these tools for free with Starting Point, our beginner-friendly introduction to Hack The Box (HTB) Labs. I completed tier 0 of Starting Point while writing this post and learned a lot about the techniques, services, and misconfigurations related to the tools in this list.
Pentesting tools vs. techniques: why beginners need to think beyond tools
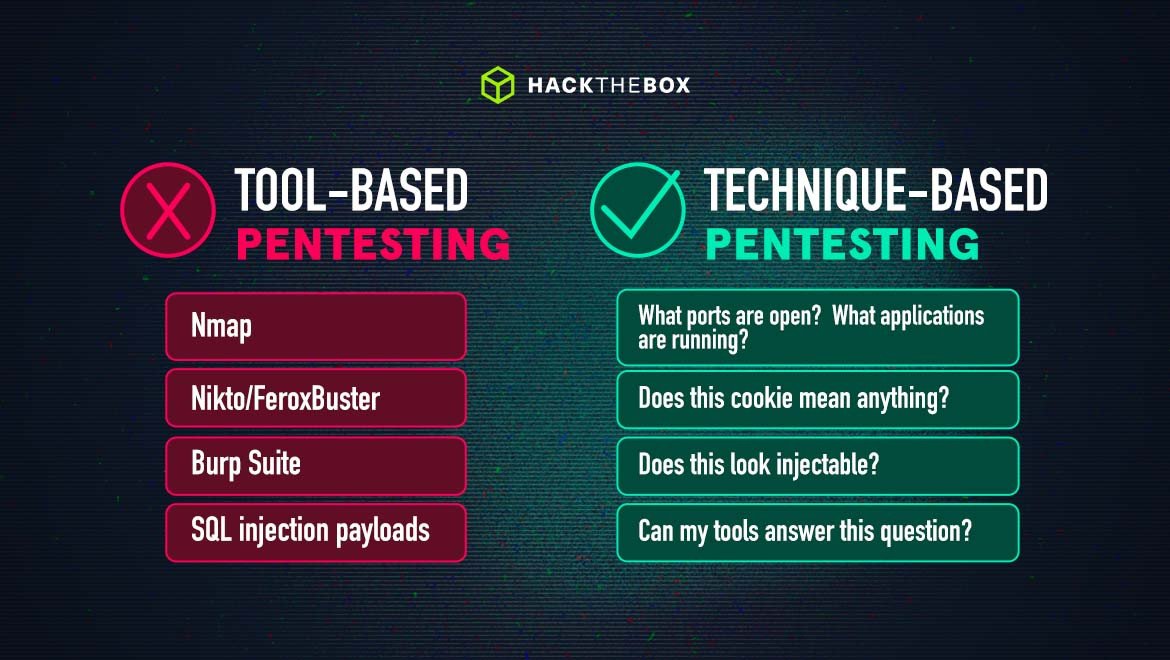
As Ippsec shared during the University CTF talks last year: when beginners get into the testing side of security, they usually default to a linear, tool-based problem-solving workflow. They’ll run Nmap, see a web server, and then run “web-servery” tools like Nikto, Gobuster/FeroxBuster. Then they’ll see a login page and run SQLmap to see if it’s SQL injectable.
This tool-biased thinking makes pentesting harder than it should be. Because as someone who’s searching for vulnerability, you’re looking for a needle in a haystack. And running tools for the sake of it shrouds that needle in information and outputs that you might not need.
Real-world penetration testing requires an element of raw human intuition. If human intuition wasn’t needed, then paid software would have solved security by now. This shows that you can’t rely on programmatic or tool-oriented thinking because creativity, adaptability, and out-of-the-box thinking are critical.
It's why a technique-based workflow that’s built on questions is more useful—you “narrow down the haystack,” read between the lines, and diagnose why steps along the attack path fail.
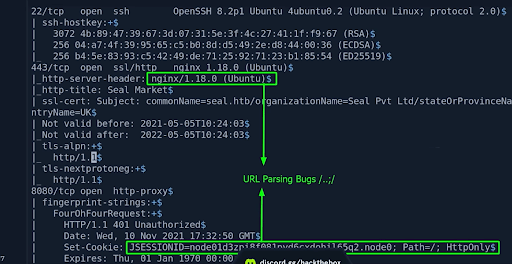
Going back to Ippsec’s talk, let's say we have a bunch of Nmap outputs:
The key things here to highlight are the Nginx server header and then the JSESSIONID. When you see engines Nginx and Tomcat, chances are there’s going to be some type of URL parsing bug.
This is an example of reading between the lines and asking ourselves questions—as the output of Nmap itself doesn’t directly tell us there’s a potential bug or vulnerability.
With that said, let’s move on to the actual tools you should familiarize yourself with if you’re new to pentesting.
7 powerful pentesting tools for beginners (with learning resources to practice them)
Linux
Learning Linux operating systems is an inevitable step for aspiring cybersecurity professionals as it offers a broad toolkit that covers many aspects of hacking. This includes tools like Nmap for network scanning, Wireshark for packet analysis, or Hashcat for password cracking (all of which run on Windows systems too).
Resources for learning Linux:
-
The free Linux fundamentals module on the HTB Academy.
-
Network Chuck’s video introduction to Linux.
-
HTB Starting Point to familiarize with commands and services using the Linux command line.
-
The beginner's bible on learning how to hack.
Nmap
Nmap is a staple in cybersecurity and one of the first tools pentesters will use to enumerate networks. It’s widely used for network reconnaissance, vulnerability assessment, and security auditing.
Using Nmap, you can send packets to target hosts and analyze their responses using various scanning techniques/protocols such as TCP, UDP, and ICMP to probe hosts and discover information about their network structure, open ports, running services, and even operating systems.
Nmap can also detect firewall rules, packet filters, and intrusion detection system (IDS) configurations to reveal the security posture of a network.
💡Note: I highly recommend playing the free Starting Point Machine, Meow, if you're completely new to Nmap and network enumeration.
It’ll guide you through the basics of network enumeration and teach you how to start thinking about identifying services, gaining access to credentials, and getting a foothold to start attacking misconfigured services on networks.
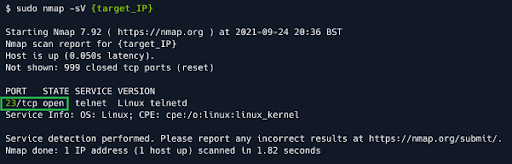
While playing Meow I see that port 23 is open after running Nmap (using the
-sVflag tells me what version of the service is running and might help me find common misconfigurations or vulnerabilities within that version).
A target is using a remote management service called Telnet, which can receive connection requests from a host. So the next step is to gain a foothold by authenticating myself so that I can send requests.
Following the walkthrough of the Machine, I’m then introduced to the basics of how brute-force attacks—and the configuration mistakes that enable them—work. It was a ton of educational fun for a noob like me!
Resources to learn Nmap:
-
Network enumeration with Nmap on the HTB Academy or our Starting Point Machines.
-
The Jeeves Machine on the HTB Labs platform which teaches you enumeration techniques to locate the correct escalation path.
-
Ippsec’s walkthrough of the Jeeves Machine. It shows how effective enumeration can speed up your ability to get admin and infiltrate a network.
Metasploit Framework
As one of the first real public offensive toolkits Metasploit Framework has been around for decades and is an open-source network pentesting tool that simplifies the act of attacking a network.
It allows users to pick a target, choose an exploit, select a payload to drop, and fire at will. The tool was originally released in 2003 and was written in Perl. It got rewritten to Ruby in 2009 and while it is still in Ruby today, it supports many other languages such as Python.
Metasploit Framework is also used for evading detection, performing privilege escalation attacks, and performing post-exploitation. There are now a massive number of exploits in Metasploit’s collection, with new exploits added frequently.
It’s worth noting that when new exploits are added to Metasploit Framework, they often undergo better quality assurance testing when compared to a random exploit on GitHub (that can be uploaded by anyone), so are less likely to inadvertently damage a system.
Resources to learn Metasploit Framework:
-
The Metasploit Framework module on the HTB Academy.
-
0xdf’s write-up of our Lame Machine: a beginner-friendly Machine that’s compromised via a Metasploit script directly to a root shell.
-
Haktool’s video walkthrough of the Lame machine which shows how to compromise the box with and without Metasploit.
Burp Suite
Burp Suite is a Swiss army knife for web app pentesting and is a common web proxy that enables testers to intercept, inspect, and modify the traffic that passes between browsers. The tool has an excellent user interface for its various features and even provides a built-in Chromium browser to test web applications.
While certain Burp features (such as faster brute-forcing/fuzzing or the ability to automatically modify HTTP messages) are only available in the paid version, Burp Suite Professional, the free community edition is still extremely useful for pentesting. It allows you to:
-
Intercept and modify requests/responses when interacting with web apps.
-
Capture, modify, and resend the same request multiple times.
-
Identify and decode recognizable encoding formats, such as URL encoding.
-
Compare any two items of data and identify subtle differences between requests or responses.
In our HTB Academy module on using Web Proxies, we cover many of the features in the community free version of the tool and also demonstrate how to use some of the paid features, like the Active Web App Scanner. There’s also a practical skill assessment included in the course that puts you in the shoes of a penetration tester conducting an internal pentest.
Tip: If you have an educational or business email address you can apply for a free trial of Burpsuite Professional.
Resources to learn Burp Suite:
-
The Web Proxies and Web Requests modules on the HTB Academy.
-
The Writer Machine on the HTB platform which covers techniques such as SQL injection, Server Side Request Forgery (SSRF), and local file incursion.
-
Ippsec’s walkthrough of the Writer machine.
Wireshark
Wireshark is a network protocol or packet analyzer that allows for capturing, analyzing, and interpreting network traffic in real time or from stored capture files. It helps users inspect network traffic for security auditing, troubleshooting, and network analysis purposes.
One of Wireshark’s main features is its powerful filtering capabilities. Users can apply filters based on criteria such as IP addresses, protocols, ports, and keywords to selectively view and analyze specific network traffic of interest.
Often, pentesters will switch back and forth between Nmap and Wireshark. Nmap to see the network, and then Wireshark to see the data in the network. But they’re completely separate applications and Wireshark can be used on its own if you don’t need to do any network mapping for a particular task.
Resources to learn Wireshark:
-
An intro to Network Traffic Analysis on the HTB Academy.
-
A forensic challenge on our main platform called Chase, in which suspicious activity leads to a network capture before shutting a server down to take a clone of a disk. You’ll be tasked with analyzing the Packet Capture (PCAP) file to see if anything looks suspicious.
-
Cryptocat’s video walkthrough of the Chase challenge.
Hashcat
Cracking passwords on real-world engagements requires an understanding of the various ways that passwords are stored, how they can be retrieved, methods to crack weak passwords, ways to use hashes that cannot be cracked, and how to hunt for weak/default password usage.
Hashcat is a go-to password-cracking optimized for GPUs (fast) and rule files that make it good at building wordlists. By comparison, John The Ripper (another password-cracking tool) can crack a lot more things, but it's not as customizable or fast as Hashcat.
Resources to learn Hashcat:
-
The Password Attacks and Cracking Passwords With Hashcat modules on the HTB Academy.
-
The Armageddon Machine on our main platform in which an exploitable Drupal website allows access to the remote host. During enumeration, you’ll have to use Hashcat to decrypt a password and SSH into the remote host.
-
Ippsec’s walkthrough of the Armageddon Machine.
BloodHound
BloodHound is an open-source tool used by attackers and defenders alike to analyze the domain security of Active Directory (a directory service for Windows network environments used by many organizations).
Access management in Active Directory is complex, and it is easy to introduce vulnerabilities or bad practices in day-to-day configurations. Using graph theory, Bloodhound visually represents the relationship between objects and identifies domain attack paths that would have been difficult or impossible to detect with traditional enumeration. This helps you:
-
Thoroughly explore access control lists (ACLs), which are used by Active Directory to manage user account privileges.
-
Acquire Active Directory configuration information which can help with privilege escalation.
-
Output visual information of networks with Active Directory to explore relationships, connections, and Active Directory domain administrators.
Resources to learn BloodHound:
-
The introduction to Active Directory and Active Directory Enumeration & Attacks Modules on the HTB Academy.
-
The Forest Machine on the main platform, which focuses on exploiting an Active Directory network and features a Windows Domain Controller (DC) for a domain in which Exchange Server has been installed.
-
Ippsec’s walkthrough of the Forest Machine.
Go beyond tools. Build real skills and knowledge
The best way to learn these tools is to get your hands dirty and practice in realistic environments. No amount of theory can replace practice.
We recommend pairing the cybersecurity training courses on the Hack The Box (HTB) Academy (which feature interactive skill-building exercises) with playing HTB Machines to develop a deeper understanding of the pentesting techniques and methodology behind specific tools.
Finally, if you’re preparing for real engagements and want to become a job-ready pentester, check out our Certified Penetration Testing Specialist (CPTS) certification.
|
Author bio: Hassan Ud-deen (hassassin), Content Marketing Manager, Hack The Box Hassan Ud-deen is the Content Marketing Manager at Hack The Box. Combining thought leadership and SEO to fuel demand generation is his jam. Hassan's also fascinated by cybersecurity, enjoys interviewing tech professionals, and when the mood strikes him occasionally tinkers within a Linux terminal in a dark room with his (HTB) hoodie on. #noob. Feel free to connect with him on LinkedIn. |