Operation Tinsel Trace: practice your DFIR skills with festive-themed Sherlocks
Join the upcoming festive HTB event and protect the North Pole from cyber attacks!
Table of Contents
Of all things cybersecurity, what fires up your festive spirit into a roaring blaze that can bulldozer challenges in your way? This Christmas, we have the answer ready for you: unraveling the mind-bending mysteries behind cyber incidents that threaten Christmas itself!
Don your detective hat and jump on Sherlocks, our new investigation-based labs. You’ll focus on defensive security domains such as digital forensics, incident response, threat hunting, SOC, and malware analysis. All for a one-of-a-kind festive-themed adventure—not only for aspiring blue teamers but for anyone interested in simulating real-world attacks…
Operation Tinsel Trace
Operation Tinsel Trace consists of five exclusive Sherlocks following the compromise of Father Christmas’s festive operations by a formidable, infamous adversary: The Grinch!
As the festive season approaches, the North Pole is buzzing with activity. But not all is merry in Santa's workshop as a series of sophisticated cyber attacks threaten to disrupt Christmas.
In Operation Tinsel Trace, you will impersonate Santa's chosen elf to lead the cybersecurity response team and unravel the tangled tinsel of these incidents.
-
OpTinselTrace-1: Insider threat (Dec 17, 2023)
-
OpTinselTrace-2: S3 exposure and theft (Dec 18, 2023)
-
OpTinselTrace-3: Memory forensics (Dec 20, 2023)
-
OpTinselTrace-4: Printer compromise (Dec 21, 2023)
-
OpTinselTrace-5: Ransomware (Dec 23, 2023)
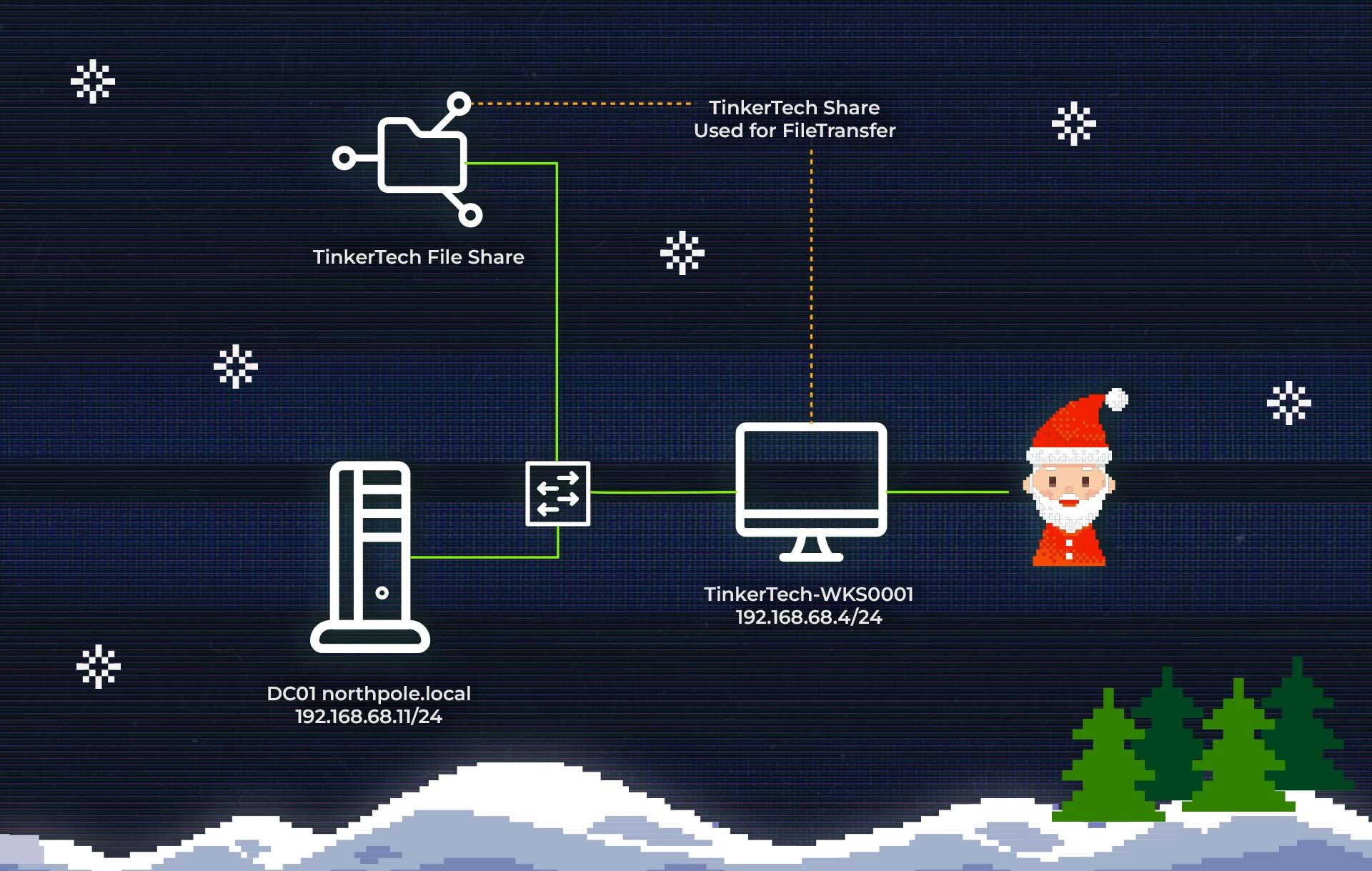
It all starts with an elf named "Elfin" acting rather suspiciously lately. He's been working at odd hours and seems to be bypassing some of Santa's security protocols. The Grinch got a little bit too tipsy on egg nog and made mention of an insider elf! You will start by running an audit of Elfin’s workstation and email communications.
Operation Tinsel Trace will lead you inside the technology of Santa’s tech, configuration, logs, and servers until, at a certain point, everything seems to be doomed. Will you be able to recover from this advanced attack?
A free festive event for all!
As mentioned, each Sherlock part of Operation Tinsel Trace will be released as part of a festive and fun-themed approach to our new defensive security labs. These special releases will be available for free to all platform members on HTB Labs until the end of December.
Join the first release on December 17th and make sure to solve this mystery before the year ends! After December 31st, all 5 Sherlocks will be accessible only with a VIP or VIP+ subscription.
Do you need another reason to participate? Well, by helping us solve this mystery, you can win some goodies right on time for Christmas!
The first three (3) platform members solving each Sherlock will get rewarded with a $100 HTB swag card, while all the wannabe Santa’s elves solving all Sherlocks within December 31st will get a 15% discount on the annual VIP+ subscription to keep practicing without worries on more than 400 labs!
How to play Sherlocks
Even if Operation Tinsel Trace shows a fictitious scenario, all Sherlocks are based on real-world cyber incidents with related attacks, methodologies, and techniques.
1. Understand the scenario
In any incident, we always say “context is king”. Reading the scenario, understanding what has occurred, and what you are investigating before starting any analysis is the correct practice to follow.
This is also a great opportunity to deeply engage with the situation you are in. We have built Sherlocks to be as realistic as possible, and therefore the scenario is extremely important!
2. Work your way through the data
What follows is the right phase to start analyzing the provided artifacts!
Download the zip file, unzip it using the provided password, and get an understanding of the clues you have been provided with.
At this stage, it's worth taking notes of what tools you might need. A simple CLI would suffice for some Sherlocks, whereas for others, you may need to call on the help of Zimmerman’s Tools or install a local SIEM instance such as Splunk or ELK.
3. Unravel the mystery
You understand the scenario, and you have analyzed the data. Next, we need to answer the key questions within the Sherlock!
As you answer the relevant questions the mystery of how the compromise, breach, or attack has happened will be gradually clear.
How to get started with Sherlocks
Jesse (aka JXoaT) will show you how to get started with our new Sherlocks in a few steps. Follow this guided video and start your investigation!
Operation Tinsel Trace for security teams
We are sure you won’t wish for something like this to happen to your organization, but it could. The average cost of an attack is about $2.5M. At the same time, companies find it challenging to source and retain talented security professionals.
All Sherlocks are mapped to the NIST/NICE framework—focusing especially on the Identify, Detect, and Respond pillars—making it easier than ever to build a skills development path following the main industry threats and how to detect techniques, tactics, and procedures used by real adversaries.
All the upcoming festive-themed Sherlocks will be available on our business plans and can become the perfect way to engage a security team right before the festive season.
We will send a special present to all teams completing Operation Tinsel Trace before December 31st! Access your workspace or get in touch to get started.