Gamifying tabletop exercises: 5 steps for effective TTXs
Tabletop exercises (TTXs) can be a total snoozefest. What if you could turn them into thrilling, edge-of-your-seat experiences that'll have your team begging for more?
Table of Contents
Start with an injection. Say what you’re going to do. And look at the processes around that.
The problem with this approach to tabletop exercises (TTXs)?
You’re not rigorously testing any critical processes and skill sets! Not to mention that traditional TTXs can be quite the snoozefest.
After suffering “death by hundreds of boring TTX PowerPoint slides” in my consulting and senior analyst roles, I turned to gamification to stress-test technical skills and processes.
The difference in team engagement was night and day: staff became more actively involved, discussing and collaborating on technical problems.
This led to a deeper understanding of technical subject matter and painted a more realistic picture of the incident response performance, skills, and processes.
In this post, I’ll show you how to tap into the playful side of your team's brain and transform mundane incident response exercises into immersive and memorable learning experiences.
What are tabletop exercises (TTXs)?
Tabletop exercises (TTXs) are proactive cybersecurity simulations designed to test an organization's incident response capabilities and cyber-specific SOPs.
During these exercises, various teams, including (but not limited to) cybersecurity professionals, information security teams, and risk management experts, come together to respond to simulated security incidents.
TTXs are crucial for improving incident response (IR), strengthening security preparedness, and fostering team collaboration.
Related read: Implement a cybersecurity workforce development plan with HTB.
Benefits of tabletop exercises for cybersecurity
-
Strengthened incident response: TTXs provide an opportunity to practice and refine incident response processes. Teams with different roles and responsibilities to stress-test their ability to respond appropriately during real security incidents.
-
Enhanced security preparedness: TTXs help identify vulnerabilities and weaknesses in an organization's security posture by simulating diverse attack scenarios, allowing for proactive measures.
-
Better team collaboration: Involving cross-functional teams in TTXs encourages better communication and coordination, resulting in a more cohesive and effective response strategy.
-
Risk mitigation and compliance: Identify potential compliance gaps and proactively address them, minimizing risk and ensuring adherence to industry standards. This helps organizations avoid costly penalties and maintain a strong security posture. It also allows teams to modify their SOPs and enable predictive mitigation measures.
Recommended read: SOC analyst interview questions (answered by an ex-analyst).
The solution to boring tabletop exercises
Challenges in traditional incident response TTXs can be summed up in three key points:
-
Limited engagement and motivation: Participants often find these exercises lacking excitement and may view them as mere “checkbox” activities. There’s definitely room for a stress-testing process and skills within TTX exercises which often last an eight-hour period.
-
Limited interaction: In many cases, the exercises lack opportunities for meaningful interaction among participants, leading to a lackluster experience.
-
Difficulty in measuring progress: It can be challenging to assess the success or effectiveness of TTXs, especially when the focus is primarily on theoretical scenarios.
The solution?
Using gamification to stress-test technical skills and processes.
Gamification involves adding practical exercises and interactive challenges to create a more engaging and enjoyable TTX experience.
How to design technical (and fun) TTXs that have an impact
While some incident response tabletop exercises may avoid technical aspects, I firmly believe that technical elements play a crucial role in realistic simulation and assessment.
By integrating technical challenges and scenarios using the steps below, we ensure that participants test their processes and apply technical skills in realistic situations.
Step 1: Set relevant goals and objectives for your teams
You've got to set the stage right, right from the get-go. In traditional TTXs, you might slog through a scenario while perusing an existing incident response plan.
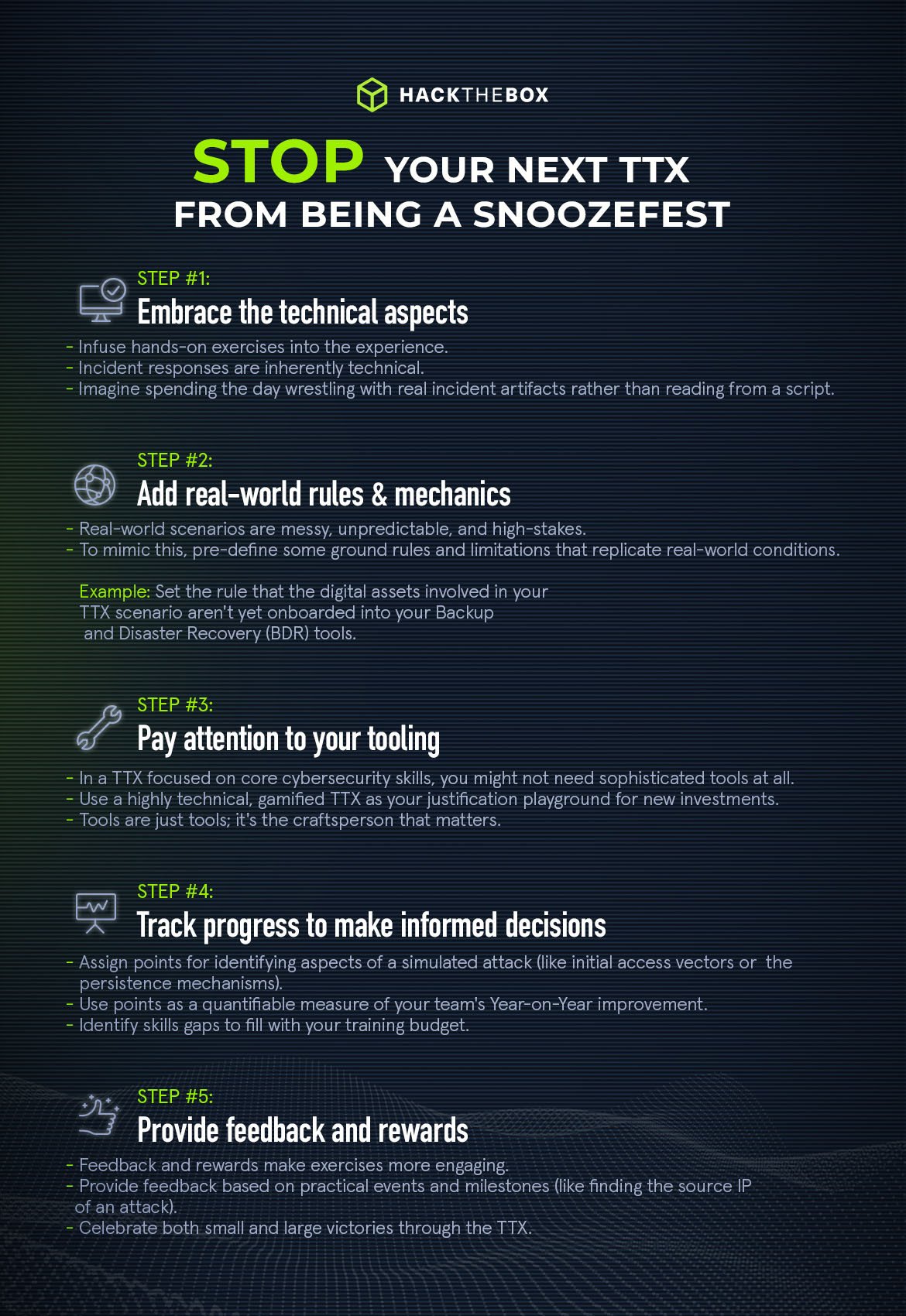
However, practical TTXs infuse hands-on, functional exercises into the experience. Imagine spending the day wrestling with real incident artifacts rather than reading from a script.
In my consulting days at Trustwave, I found that TTXs that emphasized technical elements yielded better results. And why shouldn't they?
Incident response complications are often technical.
Omitting the technical facets is like tying one arm behind your back. You're setting up a situation where the exercise doesn't reflect real-world challenges.
When you include technical elements, you better understand the weak points, both in processes and team members.
For example, your exercise objective for the day might be as specific as identifying deficiencies in your incident response procedures and playbook—a problem far better solved with hands-on troubleshooting than theoretical discussions.
Step 2: Add real-world rules & mechanics
Games have rules, and so should your gamified tabletop exercise. The traditional TTX often doesn't set the stage nicely for participants to immerse in real-world scenarios.
You're handed a script, read through a series of prompts, and go through the motions.
Here's the rub: In a real incident, you don't have the luxury of turning to page 47 of your incident response manual. Real-world scenarios are messy, unpredictable, and high-stakes. If your IR manual is over 47 pages long, then a practical TTX would probably highlight this is too long.
To mimic this, pre-define some ground rules and limitations that replicate real-world conditions.
You might set the rule that the digital assets involved in your TTX scenario aren't yet onboarded into your Backup and Disaster Recovery (BDR) tools.
Now, participants must "live off the land," simulating the need to collect artifacts for retrospective analysis.
This rule might seem like a minor tweak, but it can deeply change the dynamics of your exercise and make it considerably more challenging and practical.
Step 3: Pay attention to your tooling
Selecting tools for a TTX isn't straightforward. You can't just slap on a universal tool like Splunk, Elk, or Grey Log and call it a day.
The ideal approach?
Customize your tooling according to the requirements of your organization. The world really is your oyster on this. Here’s some inspiration:
Balance tooling and skills
There's this misconception that more advanced tools make for a better TTX. Wrong.
In a TTX focused on core cybersecurity skills, you might not need sophisticated tools at all.
Let's consider this through the lens of a real-world example. During a TTX I facilitated for a large client, we ran the exercise in a non-fault environment we set up in Amazon Web Services (AWS) infrastructure, integrating it with Cyber Reason—this company's extended detection and response (XDR) tool of choice.
The simulated attacks triggered real-time alerts, creating an immersive training ground that had zero impact on the company's actual operations.
Tool testing and decision-making
Here's the kicker: TTXs offer an exceptional platform to evaluate tools you're considering for your organization.
Say you're the CISO and mulling over a big investment. A highly technical, gamified TTX is your justification playground.
Once, I helped an organization set up a TTX where we A/B tested two potential XDR tools—Cyber Reason and Sentinel One.
We measured not just the tools' performance but how comfortable the cybersecurity analysts were in using them.
So, you're not only making informed tool choices, you're future-proofing your team's adaptability.
Identify where training budgets should go
Let's not get lost in the maze of tooling. You're missing the point if you get too focused on the gadgets. Core skills are the bedrock upon which any cybersecurity specialist should stand.
Once those are solid, tooling becomes the cherry on top.
In another TTX I ran, we minimized tooling to focus on participants' foundational skills.
That focus allowed us to identify critical gaps in areas like malware reverse engineering, thus indicating where to allocate the budget for further training.
During another memorable TTX for a sizable client, we employed their Cyber Reason tooling in a fault-free environment.
Technical teams performed real-time incident responses, and their analyses directly influenced managerial decisions—from issuing media statements to isolating compromised systems.
This holistic approach engaged both technical and non-technical teams, bringing a new level of realism and impact to the exercise.
Your TTX tooling strategy should be as unique as your organization. Experiment, test, and, most importantly, develop those irreplaceable core skills.
After all, tools are just tools; it's the craftsman that matters.
Step 4: Track progress to make informed decisions
This one is a game-changer, both literally and metaphorically. Ensure points are assigned for identifying or responding to events that occur—technical or non-technical.
Specific points may be assigned to “Production of a communications statement” in response to a data breach affecting the customers of your organization. In the production of the exercise, a “perfect” response can be formulated based on the type of attack and expected actions by the playing team.
One year, your team might detect the data exfiltration and confirm the data that's been exfiltrated. In tandem, your media/comms team produces a communications plan that satisfies both partners and customers.
You may however have missed the importance of isolating the asset in time and forgot to effectively disrupt the exfiltration. This might assign you 70 out of the possible 90 points. Next year the goal would be to ensure your processes are effectively updated so you don’t forget this important step!
This is an extremely effective and quantifiable way to measure your team's year-on-year improvement, always aiming for that grand 100% response score.
Step 5: Provide feedback and rewards
Look, if you're spending an entire day on an exercise, it better be engaging. In the conventional setups, all you'd hear is, "Great, you've done that correctly."
But practical feedback elevates this experience to another level. For instance, when you analyze server logs and find the source IP of an attack, there's a genuine buzz in the room.
That's a win right there, and you should celebrate those small victories to keep teams motivated.
Make cybersecurity upskilling more enjoyable
I always think ”what would make this fun?”
We don't need to turn our TTXs into an episode of Cocomelon, but let's ensure they're engaging.
Gamification doesn't mean frivolity; it means sustained engagement and realistic simulations.
Let's incorporate these elements into our TTXs to make them not just a regulatory "checkbox," but a genuinely useful exercise that readies us for real-world cybersecurity challenges.
Speaking of realistic challenges, if you’re aiming to strengthen your defensive posture and close potential gaps in detection capabilities, check out HTB’s selection of cybersecurity labs and guided content for SOC teams.
|
Author Bio: Sabastian Hague (sebh24), Defensive Content Lead, Hack The Box Sabastian Hague is a seasoned cybersecurity professional with over eight years of experience in the field. After serving in the Royal Air Force as a specialist in all things SOC, he went on to work for Vodafone's global CERT team before taking on a role as a senior security consultant with SpiderLabs and working on numerous high-profile incidents. He is now the Defensive Content Lead at Hack The Box. Seb has numerous industry certifications including GIAC Certified Detection Analyst (GCDA), GIAC Continuous Monitoring Certification (GMON), GIAC Certified Incident Handler (GCIH), GIAC Certified Intrusion Analyst, Offensive Security Certified Professional (OSCP), Blue Team Level 1 (BTL1), Blue Team Level 2 (BTL2), Cybereason Threat Hunter (CCTH). |