An (aspiring hacker’s) web application penetration testing guide for 2024
Our 2024 guide on web application penetration testing is perfect for beginners. Learn to identify vulnerabilities, exploit weaknesses, and report findings ethically.
Table of Contents
- What is web application penetration testing?
- Benefits of web application pentesting for organizations
- Types of web application pentests
- Internal vs. external web pentesting
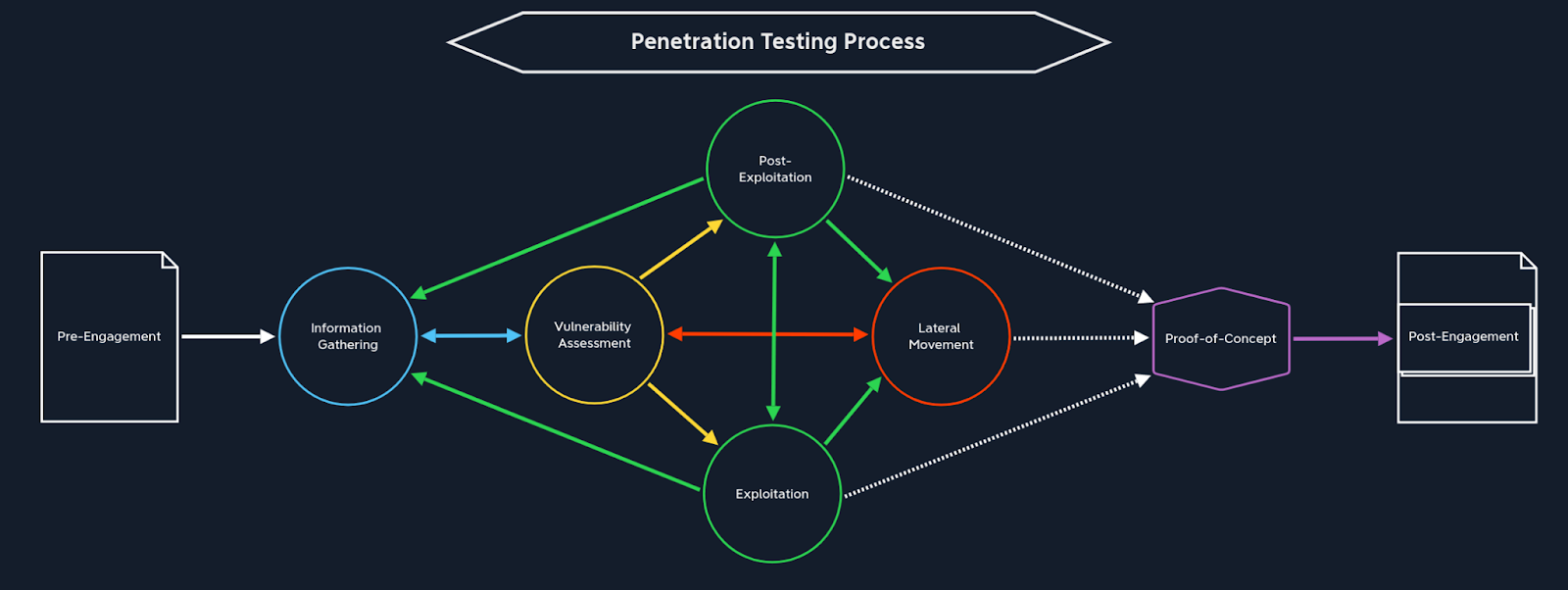
- The web app penetration testing process
- Tools for web application penetration testing
- Become a web app pentester:
- Learn Python on the HTB Academy
- The path of the righteous: HTB job role paths
Imagine receiving an email from cybercriminals stating that all your personal information has been compromised—name, date of birth, home address, and finances. They are demanding money from you in exchange for not leaking your sensitive information.
It's a terrifying situation to be in, isn't it?
This is exactly what happened during the MOVEit breach in May 2023. Cybercriminals (the Clop ransomware gang) exploited a vulnerability in a file-transfer service that affected thousands of organizations and at least 60 million individuals.
On a more personal note, my talent team recently performed a penetration test on a highly regarded institution that is very diligent in protecting hundreds of critical records and documents.
Although their primary concern was to ensure confidentiality, the team discovered a tiny detail in the web application that could delete all records from the outside instantly.
These are glaring testaments to what can go disastrously wrong when web application security isn't respected.
Enter: Web application penetration testing.
Editor's note💡: One of the biggest data breaches on record emerged at the time of writing this piece. Named the Mother of All Breaches (MOAB), 26 billion records are reported to have been leaked from apps like Dropbox, LinkedIn, and Twitter.
What is web application penetration testing?
Web application penetration tests are proactive security assessments that evaluate the security of web applications by simulating real-world attacks.
The primary goal is to uncover potential weaknesses, misconfigurations, and vulnerabilities that malicious actors could exploit to compromise the confidentiality, integrity, or availability of a web application.
Benefits of web application pentesting for organizations
The size of the penetration testing market is set to grow at a compound annual growth rate (CAGR) of 13.5%, estimated to reach USD 8.13 billion by 2030 (according to Market Research Future).
This growth reflects the sheer number of web applications that store and process vast amounts of sensitive information, and the need to invest in securing that data.
As organizations increasingly rely on web-based platforms to conduct their operations and to provide their services, web penetration testing is imperative. It’s crucial to identify, address, and evaluate the real impact of vulnerabilities before they can be exploited by malicious actors.
This helps organizations in prioritizing the identified vulnerabilities within the web application leading to the development of optimised effective strategies for their mitigation.
Going back to the MoveIT transfer breach mentioned in the introduction, a web application penetration test could’ve helped thousands of organizations potentially protect sensitive data. Or at the very least, help identify and mitigate serious security issues.
|
Compliance and regulation requirements Adding to these security concerns, certain sectors, particularly those handling sensitive customer information, mandate the inclusion of penetration testing. Specific security regulations that encompass penetration testing compliance include:
To ensure compliance, it's important to train developers to spot vulnerabilities in code and understand how attackers think, to stop threats early on. |
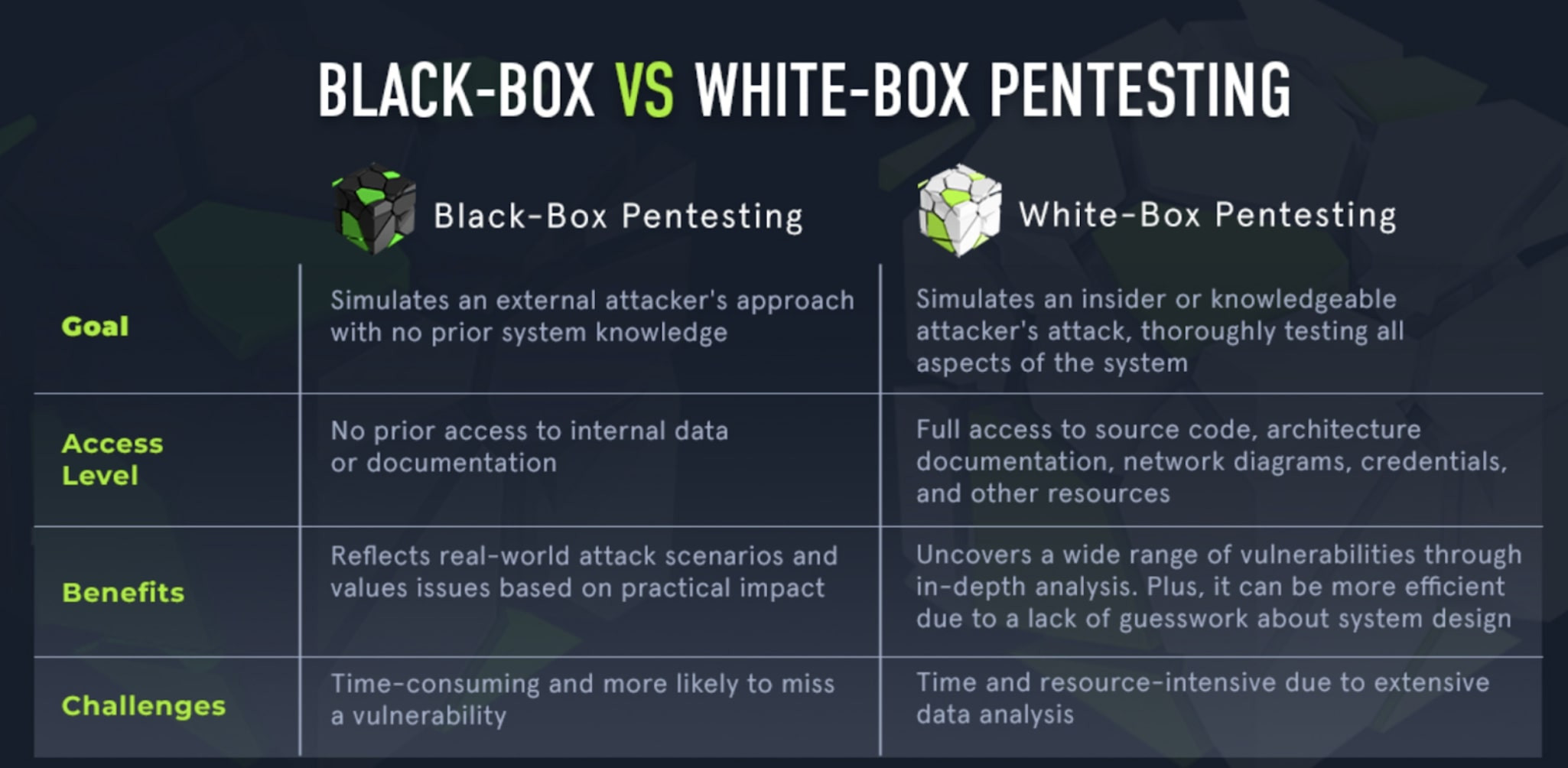
Types of web application pentests
3. Exploitation
Armed with all the information and identified vulnerabilities in the previous stages, testers are ready to rock and roll. This is where the actual “hacking” takes place.
This stage is what sets penetration testing apart from vulnerability assessments. Vulnerabilities are hands-on tested to determine their true exploitability and impact.
A diligent tester is always up to date with the latest and most prevalent web application vulnerabilities and how to exploit them, such as:
-
DoS
4. Post-engagement
Testers diligently craft comprehensive documentation intended for delivery to the client.
The standard deliverables encompass a detailed penetration testing report accompanied by a walkthrough meeting.
The report documents each action, step, command, and tool employed by the testers throughout the assessment.
This provides the client with a clear understanding of the identified vulnerabilities, their potential impact, and recommended remediation strategies.
Note💡: Hack The Box has a ready-to-use penetration testing template waiting for you. Follow this in depth guide on how to use it.
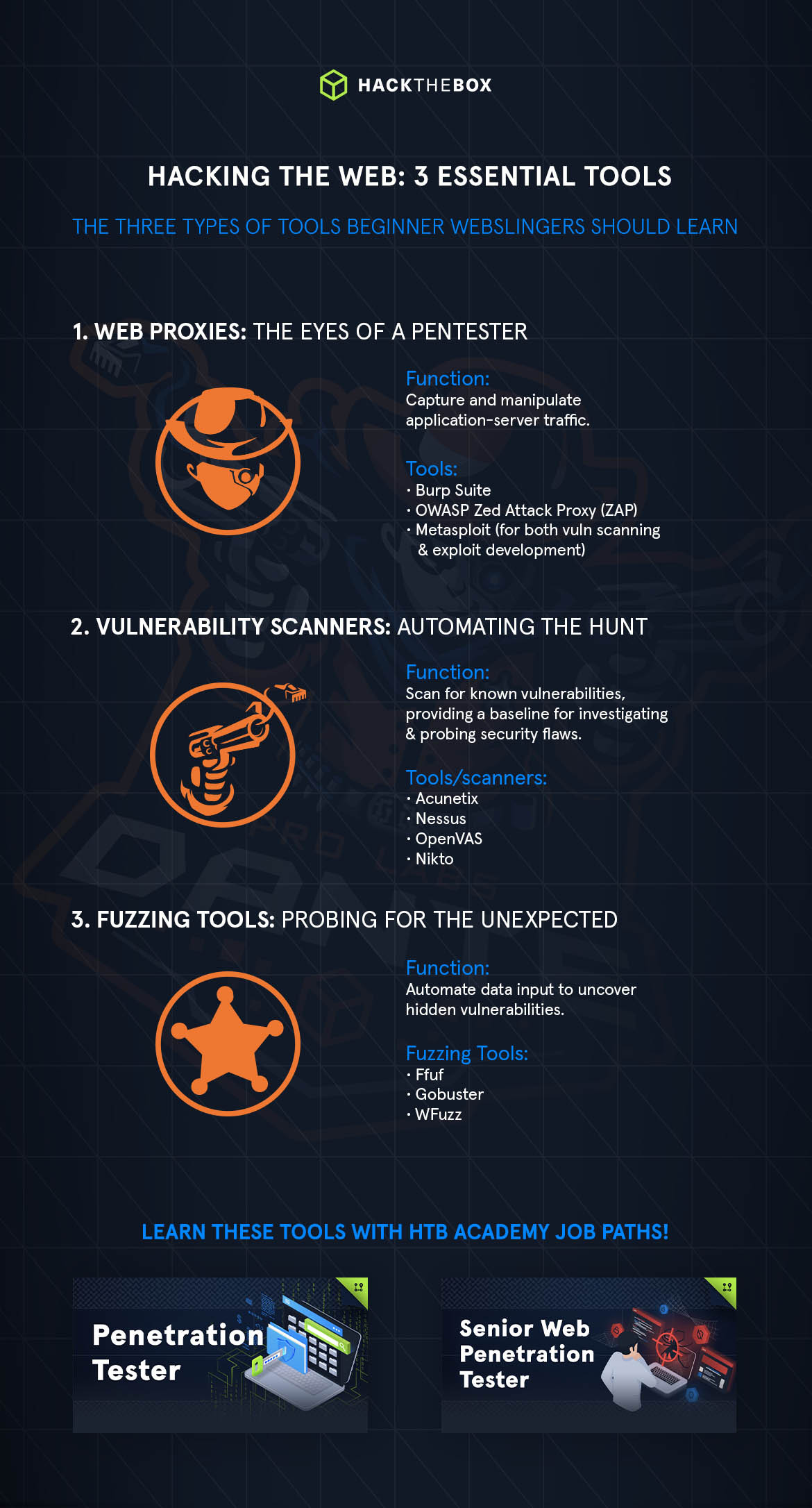
Tools for web application penetration testing
There are essential tools that any web pentester must be comfortable with to carry out tests.
Learn how to use the Metasploit Framework
This module introduces the fundamentals of the Metasploit Framework with a retrospective analysis of the usage of automated tools in today's penetration testing environments. Learn about:
-
An overview of the Metasploit Framework.
-
Metasploit module types.
-
Setting targets and payloads.
-
Pivoting between sessions and jobs.
-
Importing new modules.
-
Creating a custom payload.
-
Creating a custom module.
-
Using Meterpreter and Kiwi.
Fuzzing tools
Feeding large amounts of data into a web application can uncover unexpected vulnerabilities. That's called fuzzing.
Fuzzing can uncover weaknesses that could not be found using other tools and methods.
It can identify intricate bugs that are hidden deep inside the web application's codebase, which cannot be found by vulnerability scans or brute force content discovery methods.
Other tools include:
-
Ffuf: An open-source fuzzing tool written in Go. Helps you find hidden content on web applications.
-
Gobuster: For brute-forcing directories and files in web sites.
-
WFuzz: A tool used to discover common vulnerabilities on web applications. Written in Python.
You must also keep in mind that it's not all about automated tools! Manual testing is also fundamental.
It allows for a more granular, in-depth exploitation of web applications. Uncovering what automated tools miss or get wrong (hackers truly shine at this stage).
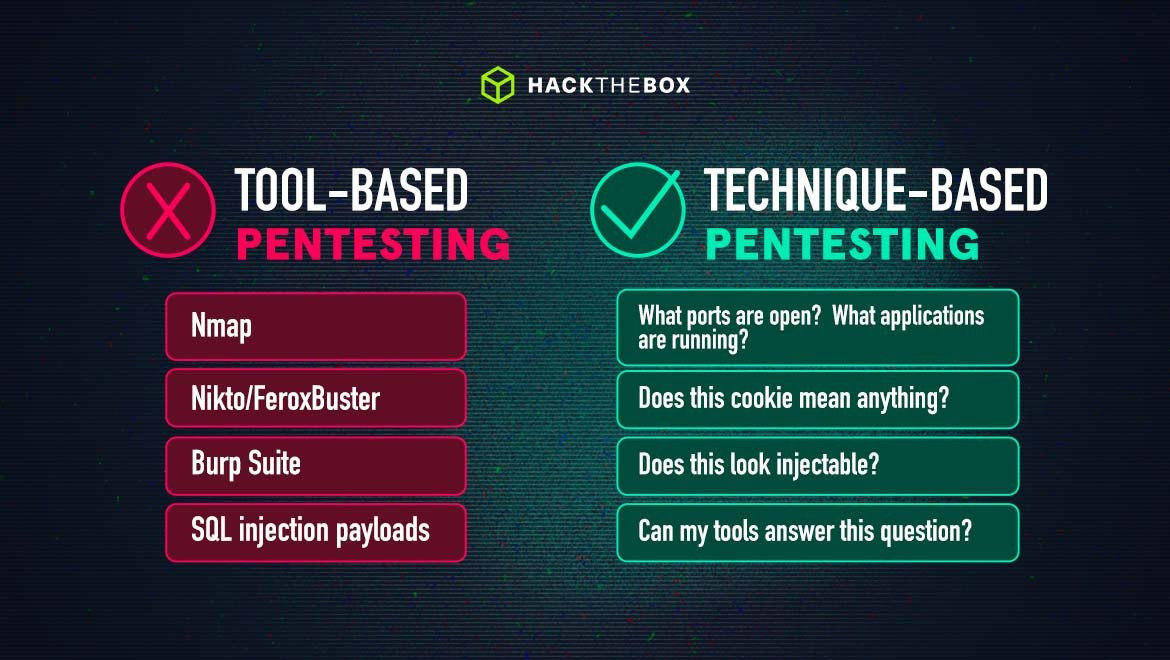
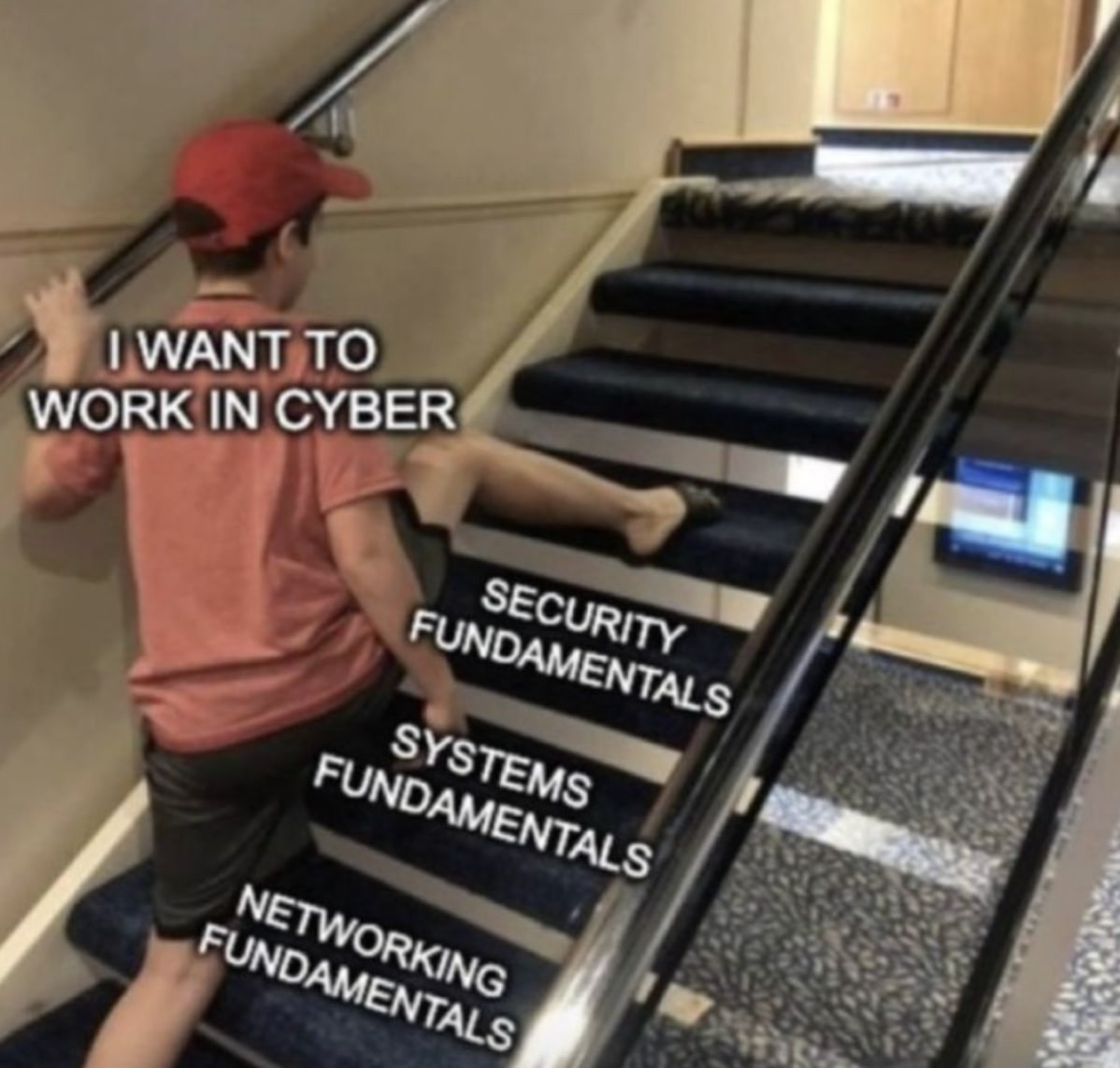
We've been talking about tools. I bet by now you are thinking "I must learn all these cool tools". Yes, you must. But learn fundamental concepts first; have a clear understanding of why you're using those tools and not how to use them.
Recommended read: 7 powerful pentesting tools for beginners (with learning resources to practice them).
Learn web application pentesting with HTB Academy

Drill down with the Web Requests module, and learn the fundamentals of web applications. This module will also introduce you to cURL and the Browser DevTools. These are essentials every penetration tester must have in their arsenal (yay, more tools!).
Follow up with Introduction to Web Applications. Learn how web applications work and have your first contact with the art of web application penetration testing.
This will be your initial encounter with common vulnerabilities found in web applications, and soon enough, you’ll be exploiting them.
After covering all the fundamentals you can start focusing your path on learning web application vulnerabilities and how to exploit them:
And here's the kicker, you don't have to sprint through these courses. Take it slow, enjoy the ride.
Eventually, you'll develop a mindset that will allow you to correlate concepts, making it easier to further develop your skills. (Trust me, this whole learning process can become quite addictive.)
The path of the righteous: HTB job role paths
Hopefully by now you'll have a more clear understanding of the basics.
If you are still overwhelmed with the amount of information or you want a more focused approach without "outside noise", consider choosing a Job Role Path on Hack The Box.
Hack the Box Job Role Paths will guide you systematically through Academy modules, equipping you with practical skills and the mindset required for a specific job role.
Consider following The Bug Bounty Hunter Job Role Path.
It’s ideal if you’re a security-minded developer, aspiring web pentester, or want to become a good bug bounty hunter. (Despite bug bounty hunting being a separate discipline from web application penetration testing, the skills necessary for both are similar.)
If you want to become a professional web penetration tester, check out the Penetration Tester job role path. Learn core security assessment concepts and a deep understanding of the specialized tools, attack tactics, and methodology used during penetration testing.
|
Author bio: Pedro Correia (g4rg4m3l), Cybersecurity Lead, Red Teamer, and Instructor at Code For All_ Pedro Correia is a cybersecurity professional with a strong commitment to both learning and teaching. He currently serves as a Cybersecurity Lead, Red Teamer, and Instructor at Code For All_. He oversees a specialized team focused on penetration testing and cybersecurity assessments, with years of experience in educating students from diverse backgrounds worldwide in the domains of cybersecurity and programming. He also creates content specializing in various cybersecurity domains under the alias of “Cybersecurity Paladin.” As a Hack The Box Ambassador, Pedro hosts meetups, showcases, and live hacking demonstrations, making cybersecurity concepts more accessible to a wider audience. You can find him on HTB as “g4rg4m3l.” Pedro has embarked on a self-imposed delusional mission to infiltrate every Active Directory environment. Join him on this crusade. Feel free to connect with him on LinkedIn. |